Fortinet CVE-2026-35616 Exploit: Patch FortiClient EMS
-20260405122140.webp&w=3840&q=75)
Hoplon InfoSec
05 Apr, 2026
What happened on April 5, 2026?
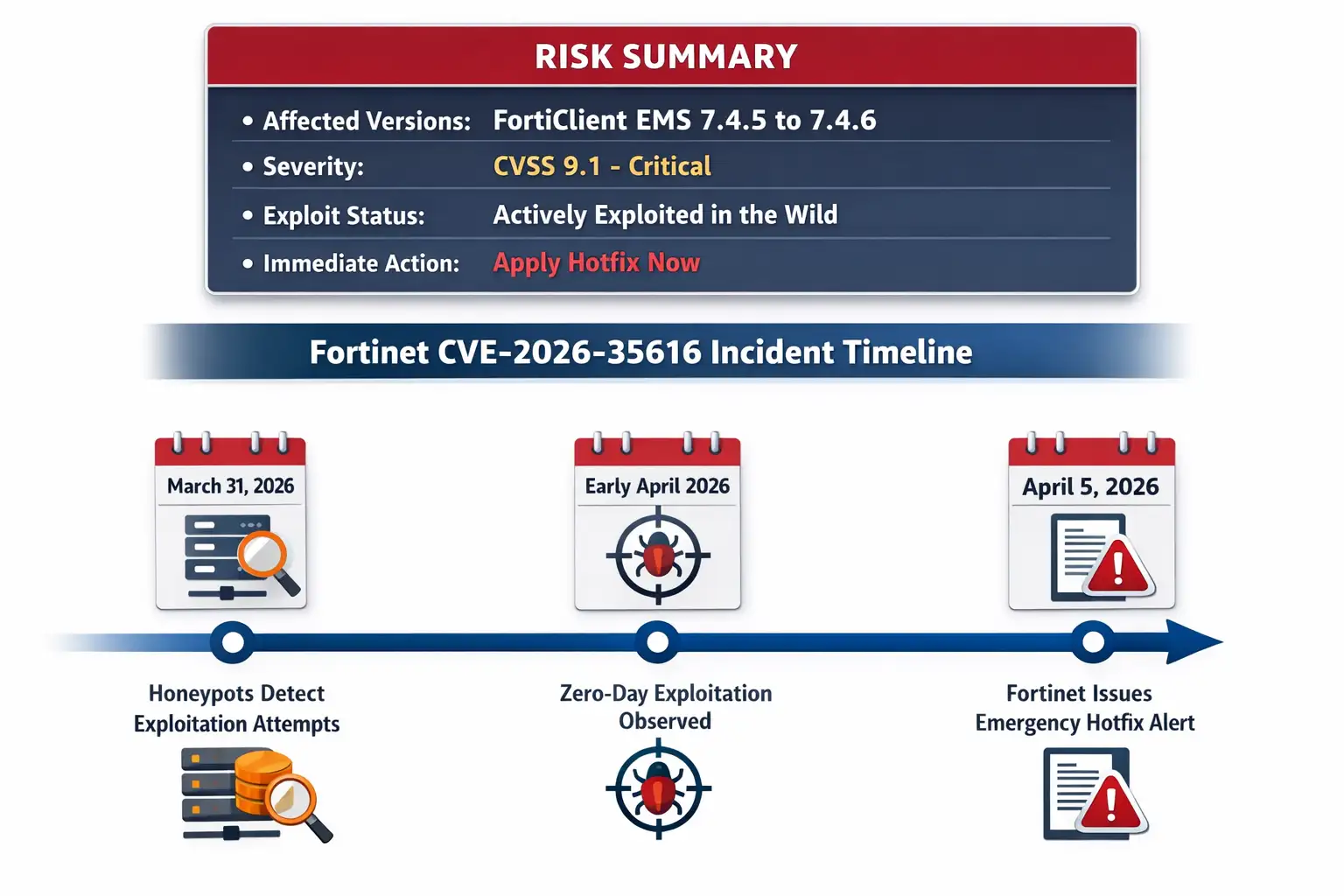
Fortinet disclosed that CVE-2026-35616 is a critical FortiClient EMS vulnerability with a CVSS score of 9.1, affecting versions 7.4.5 through 7.4.6, and said the flaw is already being exploited in the wild. The issue is described as an improper access control problem that can let an unauthenticated attacker send crafted requests and execute unauthorized code or commands. Fortinet urged customers to apply the available hotfix immediately, with a fuller patch path expected in version 7.4.7.
Why this story matters right now
When a security vendor says a flaw is being exploited in the wild, that usually changes the conversation from routine patching to urgent response. That is exactly where Fortinet CVE-2026-35616 sits today.
This is not a theoretical bug buried in a changelog. It is a live risk tied to a management platform many enterprises use to control endpoint security at scale.
FortiClient EMS is not some forgotten side tool either. It is the command center for deploying policies, managing clients, and coordinating endpoint behavior across an organization.
If a system like that is exposed to the internet, a pre-authentication weakness is the kind of thing defenders lose sleep over. One bad request can turn a neatly managed environment into a scramble of logs, containment checks, and late-night calls.
What is Fortinet CVE-2026-35616?
At its core, Fortinet CVE-2026-35616 is an access control flaw in FortiClient EMS. Public reporting says it is a pre-authentication API access bypass that can lead to privilege escalation.
That means an attacker may not need valid credentials first. If the target is vulnerable, crafted requests may let them slip past API authentication and authorization controls and then run unauthorized code or commands.
That detail matters because pre-auth bugs are usually more dangerous than issues that require an existing user account.
Security teams can sometimes contain authenticated flaws with MFA, tighter admin roles, or segmented accounts. A flaw that starts before authentication is more ruthless. It reduces the number of steps an attacker needs and gives defenders less room for error.
Affected Versions and Technical Scope
Based on current public reporting, the affected FortiClient EMS versions are 7.4.5 through 7.4.6. Fortinet has released a hotfix for those builds, and version 7.4.7 is expected to contain the complete patched state.
OpenCVE also reflects the affected product as FortiClient EMS 7.4.5 through 7.4.6 and scores the issue at CVSS 9.1, reinforcing the severity that administrators should assign to this case.
The exploit path described publicly revolves around crafted requests to the EMS API. That does not automatically mean every installation is equally exposed. A tightly isolated internal EMS server is in a better position than one left open to the internet.
Still, the moment a management plane becomes reachable from outside, weaknesses like this move from “important” to “urgent.” That difference is what makes patch discipline so important in enterprise software.
How the Exploitation Timeline Makes This More Serious
Security incidents often feel abstract until there is a timeline. Here, the timeline sharpens the risk. Public reporting says Defused Cyber observed zero-day exploitation earlier in the week, and watchTowr said its honeypots recorded exploitation attempts beginning on March 31, 2026. Fortinet then confirmed active exploitation and pushed customers toward immediate hotfixing.
That sequence tells a familiar story. Attackers appear to have moved quickly, researchers spotted activity, and defenders were left with a small response window. In security operations, those compressed windows are painful.
By the time a broader audience hears the CVE number, somebody else may already be scanning, probing, or trying to chain the flaw with weak exposure controls. That is why articles about these incidents need to go beyond “a patch is available” and spell out operational urgency.
Why FortiClient EMS Is Such an Attractive Target
Attackers like management consoles for the same reason IT teams do. They are centralized, powerful, and deeply connected to the environment. An endpoint management server is not just another app.
It often has visibility across endpoints, policy controls, software deployment functions, and trusted relationships inside the network. If compromised, it can become a pivot point, not just a single broken box.
There is also a practical reason. Security software is often granted broader trust than ordinary business apps. That means defenders sometimes focus more on what the tool detects than on how the tool itself should be protected.
It is a little like putting the safest lock in town on your front door and forgetting the side gate is hanging open. Management infrastructure deserves the same hardening attention as domain controllers, VPN gateways, and identity systems.
What Could Attackers Gain?
Public descriptions say successful exploitation may allow an unauthenticated attacker to execute unauthorized code or commands. That is already serious enough. In operational terms, it can mean remote control over part of a security management workflow, depending on exposure, privileges, and surrounding defenses.
What remains less clear in public reporting is the full post-exploitation playbook. There is not enough verified public detail yet to say exactly how threat actors are chaining this flaw after initial access, and that uncertainty matters.
Good response writing should not pretend every step is known. At the time of writing, the safest assumption is simple: if your vulnerable FortiClient EMS instance is reachable, treat this as potential compromise until proven otherwise.
How This Compares With Recent FortiClient EMS Trouble
This new issue lands only days after another critical FortiClient EMS flaw, CVE-2026-21643, drew attention for active exploitation. Public reporting has not confirmed whether the same actor or actors are behind both campaigns, and there is no verified evidence yet that the two are being chained together.
Still, the timing naturally raises concern for defenders who are already wondering whether attackers are concentrating on the same product family.
That context changes how readers should interpret Fortinet CVE-2026-35616. This is not just “one more patch Tuesday item.”
It is part of a pattern in which endpoint management infrastructure is getting real attacker attention. When that happens, patching alone is necessary but not sufficient. Organizations should also review exposure, logs, admin access, and abnormal API behavior.
-20260405122140.webp)
What Administrators Should Do Next
1. Apply the hotfix immediately
Fortinet said vulnerable customers should install the hotfix for FortiClient EMS 7.4.5 and 7.4.6 as soon as possible. That is the main defensive action supported by current public guidance.
2. Move fast on internet exposure
If your EMS instance is internet-facing, review whether it truly needs to be. Even a temporary restriction through VPN-only access, IP allowlisting, or upstream filtering can shrink the attack window while change control catches up. This is not a substitute for patching, but it is sensible risk reduction.
3. Check for signs of unusual API activity
Because public reporting points to crafted requests and API access bypass, defenders should review logs for unusual request patterns, unexpected command execution, or suspicious admin-like behavior coming from unknown sources. Public sources do not yet provide a full list of indicators of compromise, so teams should be careful not to overstate certainty when performing forensic review.
4. Treat this as incident response, not routine maintenance
One public expert comment framed the timing as especially dangerous because holiday weekends can leave security teams short-staffed. That observation rings true well beyond this one case. Delayed weekend patching has a way of becoming Monday-morning regret.
FAQ
Is Fortinet CVE-2026-35616 actively exploited?
Yes. Public reporting says Fortinet observed exploitation in the wild, and outside researchers reported seeing related activity as well.
Which versions are affected?
Current public reporting identifies FortiClient EMS 7.4.5 through 7.4.6 as affected.
What kind of vulnerability is CVE-2026-35616?
It is publicly described as an improper access control issue involving pre-authentication API access bypass that can lead to privilege escalation and unauthorized code or command execution.
What should organizations do first?
Apply the vendor hotfix immediately, review whether EMS is exposed to the internet, and inspect logs for unusual API or command execution behavior.
Research Firm Quote
Recorded Future noted in its 2026 CVE landscape reporting that actively exploited vulnerabilities demand immediate prioritization because real attacker activity changes the remediation equation from routine patching to time-sensitive risk reduction. That broader point fits this case well, even though the report is not specific to this Fortinet flaw.
Hoplon Insight Box
Recommendation 1: Patch first, investigate second, but do both on the same
day.
Recommendation 2: Pull FortiClient EMS behind controlled access if it is
reachable from the public internet.
Recommendation 3: Review recent API traffic and command activity for
anything out of pattern.
Recommendation 4: Use this incident to inventory every management
console exposed outside trusted admin paths.
Recommendation 5: Watch for updated vendor guidance, because early
active-exploitation advisories often evolve as new details emerge.
Conclusion
The reason Fortinet CVE-2026-35616 matters is not just the score, though 9.1 is bad enough. It is the mix of factors around it: pre-authentication behavior, a central management product, real-world exploitation, and a patch window that does not leave much room for delay.
That combination should make every affected organization treat this as an immediate operational issue, not a background maintenance task.
The smartest response is the boring one, honestly. Patch the system. Cut unnecessary exposure. Review logs. Document what you found. In cybersecurity, the boring moves are usually the ones that save you. And on stories like this, that is the whole game.
Trusted Sources
Fortinet’s public advisory ecosystem, Fortinet documentation, OpenCVE, and one public report from The Hacker News were used to verify the incident details and patch context.
You can also read these important cybersecurity news articles on our website.
· Apple Update,
· TikTok Warning
· Apple OS update
For more, please visit our homepage and follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well.
Was this article helpful?
React to this post and see the live totals.
Share this :