iOS Security Update: Apple Expands iOS 18.7.7 for DarkSword
-20260402124905.webp&w=3840&q=75)
Hoplon InfoSec
02 Apr, 2026
Is the iOS security update worth installing right now?
Yes. On April 1, 2026, Apple expanded iOS 18.7.7 and iPadOS 18.7.7 to more devices so users with Automatic Updates can receive protection against web attacks tied to DarkSword, a recently disclosed iPhone exploit chain. Apple’s own security notes say the fix was released on March 24, 2026, then enabled for more devices on April 1, 2026. That makes this iOS security update especially important for people who stayed on iOS 18 instead of moving to Apple’s newest platform version.
What makes this story matter is not just the patch itself, but the way Apple is delivering it. This is a backported security fix, meaning Apple is giving older-version users a direct defense instead of forcing them to jump versions first. For anyone who uses an iPhone every day, that is the kind of quiet change that sounds small until you realize it can block a real-world attack path.
What Apple actually changed
Apple’s security release page lists iOS 18.7.7 and iPadOS 18.7.7 for the iPhone XS, iPhone XS Max, iPhone XR, and iPad 7th generation. The company says the update became available for more devices on April 1, 2026, so Automatic Updates users could receive protections from DarkSword without needing to wait or manually hunt for the patch.
Apple also advises users with older software to update as soon as possible. Its support page says malicious web content can target outdated versions of iOS, and visiting a compromised website or tapping a malicious link can put data at risk. Apple says devices on the latest updated versions of iOS 15 through iOS 26 are already protected, while the strongest protections come from the latest iOS 26 release.
That detail matters because many people still think security updates are only about bug fixes or small cosmetic changes. In reality, this iOS security update is more like a locked door being replaced after someone has already figured out how to open it. You do not always see the threat, but the patch closes the window before someone else gets a chance to crawl through it.
-20260402124903.webp)
What DarkSword is
Google Threat Intelligence Group says DarkSword is a new iOS full-chain exploit that used multiple zero-day vulnerabilities to fully compromise devices. Google also says it has seen DarkSword used since at least November 2025 by multiple commercial surveillance vendors and suspected state-sponsored actors.
Reuters reported that researchers from Lookout, iVerify, and Google linked DarkSword to campaigns in Saudi Arabia, Turkey, Malaysia, and Ukraine. Reuters also noted that the malware was delivered to users running iOS 18.4 through 18.6.2 when they visited one of dozens of Ukrainian websites. That is the part that should grab attention, because the attack does not require some dramatic movie-style hack. It can ride in through normal browsing behavior.
Google says DarkSword supports iOS versions 18.4 through 18.7 and uses six different vulnerabilities to deliver final-stage payloads. The same Google report says three malware families followed successful compromise, named GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER. That combination tells us this is not a one-off nuisance, it is a mature exploit chain built for repeated use.
Here is the simplest way to think about it. A normal software bug might crash an app. DarkSword is different. It is designed to chain weaknesses together, cross security layers, and reach the point where an attacker can take control with very little interaction from the victim. That is exactly why a timely iOS security update matters more than a generic “later today” reminder.
Why Apple’s move is unusual
Apple has usually pushed users toward the latest operating system rather than maintaining older branches for long. Wired reported that Apple is now enabling iOS 18-specific fixes for millions of users who remain on iOS 18 rather than forcing an upgrade to iOS 26 first. That is a meaningful shift in tone, and it suggests Apple sees enough risk here to widen access fast.
That does not mean Apple abandoned the upgrade path. It means the company is using both doors at once. If your phone can move to the newest version, that is still the cleanest long-term route. If you are staying on iOS 18 for compatibility or personal preference, Apple is now giving you a direct shield instead of leaving you exposed while you decide.
I think that is one of the most useful lessons in this story. People often delay updates because they fear battery drain, app quirks, or the tiny hassle of a restart. Those are real concerns, but they are not equal to a web-delivered exploit chain that researchers say has been used in the wild. In this case, the convenience argument loses. The iOS security update is the safer choice.
Who is most affected
Apple’s release notes and security page show the immediate focus is on iPhone XS, iPhone XS Max, iPhone XR, and iPad 7th generation users who are still on iOS 18.7.7 and iPadOS 18.7.7. Reuters also indicated that a broader population may still be running exposed versions, and that many people do not install updates quickly.
The practical risk is bigger than the device list alone. Apple says attacks can arrive through malicious web content, which means the threat is tied to ordinary online behavior such as opening a link or visiting a compromised site. That makes the issue relevant not just for journalists, executives, activists, or high-risk targets, but for regular users who simply browse the web without thinking twice.
-20260402124904.webp)
The numbers that matter
There is one number worth repeating carefully. Google says DarkSword supports iOS 18.4 through 18.7, while Reuters says the delivered payloads were seen on devices running 18.4 to 18.6.2. That overlap matters because it shows the exploit chain was active across several point releases, not just one unlucky build.
There is also a second number that puts the scale in context. Reuters reported that iVerify and Lookout estimated 220 million to 270 million iPhones could still be running exposed iOS versions, based on public estimates. That is not a precise count of victims. It is a reminder of how many devices can sit in the danger zone when updates are delayed.
And then there is the date that matters most for users. Apple says iOS 18.7.7 was released on March 24, 2026, then enabled for more devices on April 1, 2026. If a device did not get the patch right away, that delay is exactly the gap attackers would love to exploit.
What users should do next
First, open Settings, then General, then Software Update. Apple’s support page says users should update to protect their data, and it specifically recommends the latest iOS 26 version when possible. If you are staying on iOS 18, check whether iOS 18.7.7 is available and install it without waiting.
Second, make sure Automatic Updates is turned on. Apple says the new availability expansion was designed so users with Automatic Updates could receive DarkSword protections automatically. That means this iOS security update works best when the setting is actually enabled, not just sitting there in theory.
Third, be a little more skeptical with links than usual. Apple says web-based attacks can target old iOS versions through malicious web content, and Reuters reported that the observed deliveries came through websites. The safe habit is boring, but boring is underrated in security. Pause before opening random links, especially if they arrive in messages you were not expecting.
Where the reporting leaves gaps
There is still some uncertainty in the public record. Apple confirms the fix and the broader availability, but it does not publish every operational detail about how DarkSword is delivered in the wild. Google has identified the exploit chain and its supported versions, but the full victim count is still not known. Reuters also noted that it is not clear how many iPhones are vulnerable.
That uncertainty is normal in fast-moving cybersecurity stories. What matters most is not pretending to know every missing piece. What matters is acting on the verified part, which is simple enough: the exploit is real, the patch exists, and Apple says newer software protects users from these web attacks.
Research note: Google Threat Intelligence Group described DarkSword as a “new iOS full-chain exploit.” That is a strong reminder that the threat sits above a single bug and can be reused across campaigns.
A useful way to visualize it is this simple text chart:
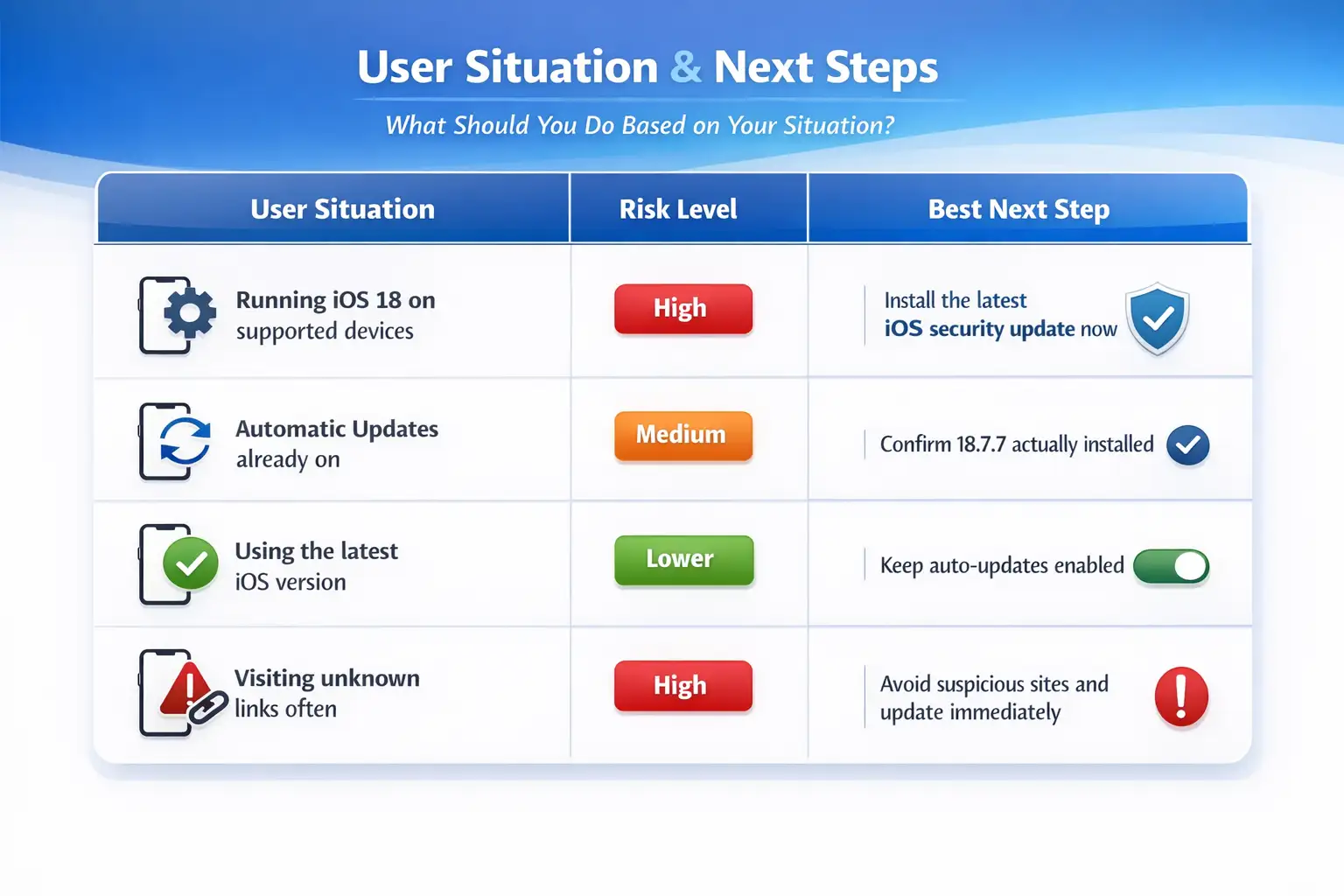 The chart is simple on purpose. This is not a case where people need a
ten-step survival manual. They need the update, a quick check that it
installed, and a little more caution around links than usual.
The chart is simple on purpose. This is not a case where people need a
ten-step survival manual. They need the update, a quick check that it
installed, and a little more caution around links than usual.
Hoplon Insight Box
What security teams and everyday users should take from this
Keep automatic updates on, verify the device actually installed the patch, and treat unknown links as suspicious even when they look ordinary. For organizations, this is a good moment to audit which devices are still on older iOS branches, because a mobile security issue like this often starts with one overlooked phone and grows from there. For individuals, the safest move is simple: install the update, then keep the habit.
FAQ
What is DarkSword in the iPhone security update story?
DarkSword is an iOS exploit chain identified by Google Threat Intelligence Group. Google says it used multiple zero-day vulnerabilities and supported iOS 18.4 through 18.7.
Which devices get iOS 18.7.7?
Apple’s security release lists iPhone XS, iPhone XS Max, iPhone XR, and iPad 7th generation for iOS 18.7.7 and iPadOS 18.7.7.
Should I update if I am already on a newer version?
Yes, if you are not on the latest software, Apple says you should update to protect your data. Apple also says the latest iOS 26 version offers the strongest security protections.
Is this a real-world threat or just a lab discovery?
It is a real-world threat. Reuters reported campaign activity in multiple countries, and Google said it saw DarkSword used by multiple commercial vendors and suspected state-linked actors.
Takeaway
The clearest lesson here is not complicated. A polished iOS security update is only useful if people actually install it, and Apple seems to know that, which is why it expanded iOS 18.7.7 to more devices on April 1, 2026. DarkSword is the kind of exploit chain that thrives on delay, so the safest move is to close that window now, not after a warning becomes a headline.
Trusted source: Apple Support security release notes for iOS 18.7.7 and Apple’s web attack guidance.
You can also read these important cybersecurity news articles on our website.
· Apple Update,
· TikTok Warning
· Apple OS update
For more, please visit our homepage and follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well.
Was this article helpful?
React to this post and see the live totals.
Share this :