Phorpiex Botnet Ransomware Attack Explained Fast
-20260403124454.webp&w=3840&q=75)
Hoplon InfoSec
04 Apr, 2026
What is the Phorpiex botnet ransomware attack, and why does it matter right now?
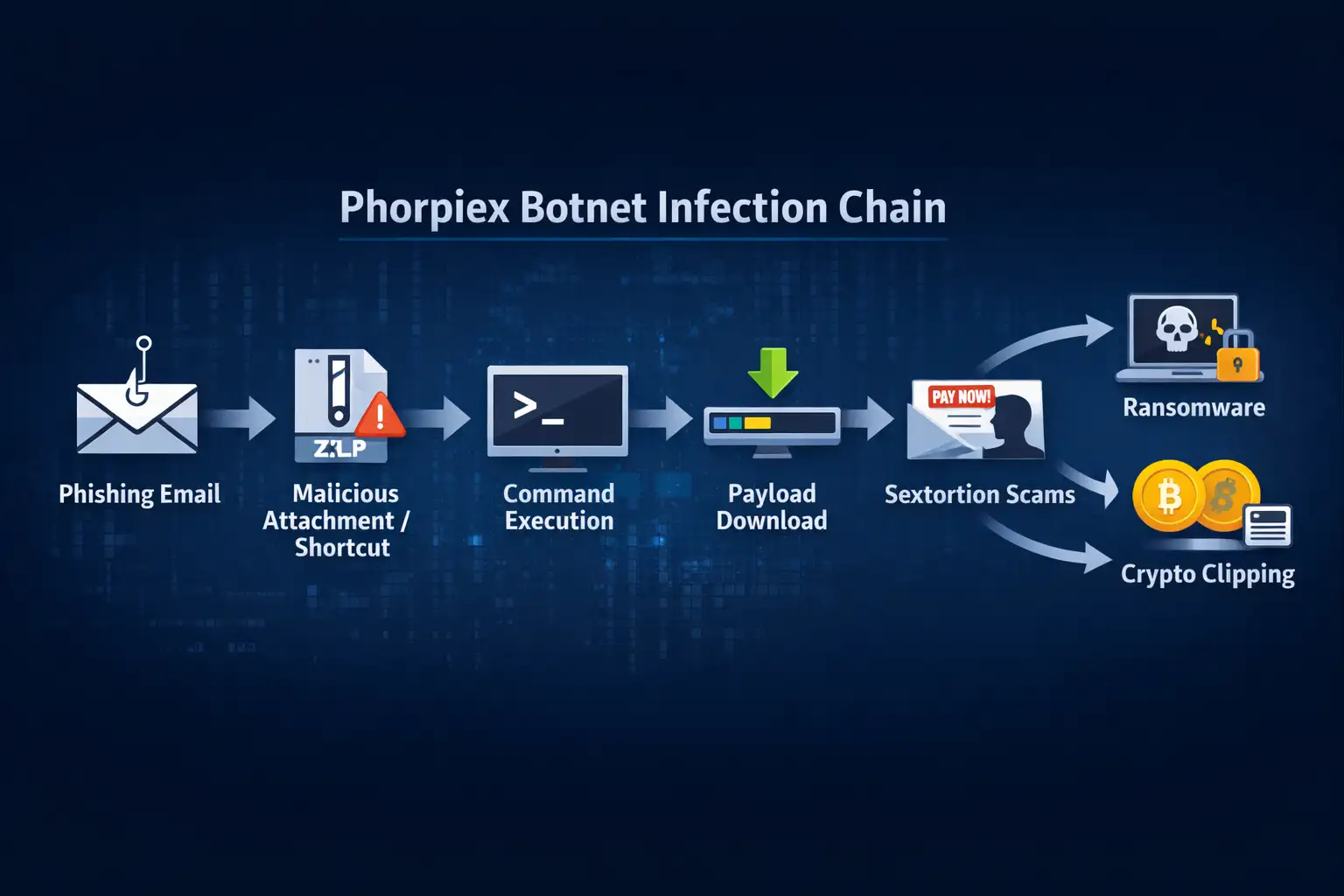
As of April 3, 2026, the Phorpiex botnet ransomware attack matters because security researchers continue to link Phorpiex to phishing-led malware delivery, ransomware deployment, sextortion email operations, and cryptocurrency theft through clipboard hijacking.
Recent reporting from Forcepoint, along with earlier research from Check Point, Secureworks, Cybereason, and CISA guidance on ransomware defense, shows that Phorpiex is not just an old spam botnet. It remains a flexible distribution system for multiple forms of cybercrime.
Phorpiex Botnet Ransomware Attack
There is a pattern in cybersecurity that shows up again and again. A threat fades from headlines, defenders relax a little, and then the same threat comes back wearing a slightly different coat. That is more or less what happened with Phorpiex botnet ransomware attack activity. For years, Phorpiex was mainly known as a noisy botnet tied to spam and large email campaigns. Now the story is wider, messier, and more dangerous.
In current reporting, researchers describe Phorpiex as a modular malware service that still helps criminals push secondary payloads, including ransomware.
At the same time, older but still relevant research connects the same ecosystem to sextortion spam and crypto clipping, which is the kind of theft that silently swaps a copied wallet address with one controlled by an attacker.
That combination matters because it shows range. One botnet can support fear-based scams, file encryption, and digital asset theft, all from a familiar infection pipeline.
Most top-ranking articles explain one slice of this problem. Some focus only on ransomware. Others stay on sextortion or cryptocurrency theft.
The real gap is the connection between those pieces. Readers need the full picture, because the risk is not one malware family doing one thing. The real issue is that Phorpiex botnet ransomware attack campaigns fit into a broader criminal model where one infection path can be reused for different profit streams depending on what the victim opens, clicks, or copies.
What is Phorpiex, Really?
Phorpiex, also known in some research as Trik, has been around for years and has repeatedly been associated with spam operations, malware distribution, and financially motivated crime.
Researchers at Forcepoint describe it as a modular malware-as-a-service botnet, while Check Point has documented its role in ransomware spread, sextortion campaigns, and cryptocurrency clipping. That long lifespan is part of what makes it interesting. This is not a one-week trend. It is an adaptable criminal platform.
The danger with long-running malware is familiarity. People hear the name once, assume the threat is old news, and move on. But old malware often survives because it keeps changing just enough to remain useful.
Phorpiex appears to be one of those threats. Check Point reported that after the original operators shut things down and sold the source code in 2021, a new variant called Twizt reappeared in a more decentralized form. That helped explain why the botnet kept showing up in later campaigns.
So when people search for Phorpiex botnet ransomware attack, they are not looking at a single isolated event. They are looking at an evolving criminal service model. That is a more serious and more realistic way to understand the threat.
How the Latest Infection Chain Works
Recent Forcepoint research described a campaign in which phishing emails used a simple lure, often something like a document-themed message, to persuade users to open a malicious Windows shortcut file. That shortcut triggered command execution, then PowerShell fetched another payload, which researchers linked to Phorpiex infrastructure. In observed cases, this chain led to Global Group ransomware.
That matters because the attack chain is not flashy. It is practical. Attackers do not always need a zero-day exploit or a cinematic breach. Sometimes they just need someone tired, busy, or distracted enough to click an attachment labeled like a harmless document. The ugly truth is that cybercriminals often succeed with boring methods because boring methods scale. Email still works.
This is one reason the Phorpiex botnet ransomware attack keeps drawing attention from researchers. It combines social engineering with automation. The victim sees a fake document. The system quietly runs commands.
The attacker gets a foothold. From there, the secondary payload can vary. That flexibility is exactly what defenders hate, because one phishing framework can feed different criminal business lines.
Why Ransomware Delivery Through a Botnet Changes the Risk
Traditional ransomware incidents often involve hands-on intrusion, lateral movement, privilege abuse, and carefully timed deployment across a network. Botnet-delivered ransomware can look different.
Cybereason noted that in one Phorpiex-related case involving LockBit Black, the ransomware delivery relied on the botnet itself to automate distribution and execution in a way that broke from the usual human-operated playbook.
That shift is important because automation lowers the barrier to scale. A botnet can hit more targets, more often, with less manual work. It also lets criminals test different lures, delivery methods, and follow-on payloads. Think of it like a criminal distribution warehouse. Once the shipment system is running, the contents of the box can change.
For businesses, this changes the response mindset. The Phorpiex botnet ransomware attack is not only a ransomware story.
It is also an email security story, a user awareness story, an endpoint control story, and a resilience story. Companies that only prepare for the encryption phase are already late. By then, the attacker has passed the more preventable stages.
The Sextortion Side of Phorpiex
One of the strangest things about Phorpiex is how comfortably it moves between technically different criminal tactics.
Secureworks and Sophos documented its role in sextortion spam campaigns, where attackers send frightening emails claiming they have compromising videos or private material and demand payment. In many of those cases, the threat is fabricated. The point is psychological pressure, not proof.
This part of the story matters because it shows that Phorpiex is not just about code. It is also about persuasion. A victim does not always need to be hacked in the Hollywood sense to lose money. Sometimes fear does the work faster than malware. A well-crafted lie can outperform a complicated exploit.
That broader criminal mix is why the Phorpiex botnet ransomware attack should be understood in context. The same ecosystem that pushes ransomware may also support extortion-themed spam, credential collection, or other profit tactics.
In practice, that means an organization or individual targeted by Phorpiex-related email activity should assume the campaign may have more than one objective.
Crypto Clipping: The Quiet Theft Most People Miss
Crypto clipping sounds technical, but the concept is simple. You copy a wallet address to send cryptocurrency. Malware watches the clipboard. The moment it detects a wallet string, it swaps that address with one belonging to the attacker.
If you do not double-check before sending, the money goes to the wrong place. Check Point’s research on the Twizt variant found support for more than 30 wallet formats and estimated theft approaching half a million dollars. Earlier research also documented long-running Bitcoin theft through clipped addresses.
There is something especially nasty about this tactic. It takes advantage of habit. Most people are careful when installing software or opening suspicious files. Far fewer people inspect every character in a pasted crypto address. That small gap between caution and routine is where crypto clippers live.
This is another reason the Phorpiex botnet ransomware attack deserves a wider lens. A victim may avoid ransomware and still lose funds.
Or a machine used for ordinary office work may later become the device someone uses for a personal crypto transfer. Security failures rarely stay inside neat categories. Real life is more tangled than that.
Why This Threat Keeps Coming Back
Botnets survive because they are useful. They provide reach, scale, and flexibility. Phorpiex has those traits in abundance. It can send spam, deliver malware, and feed different monetization strategies depending on what the operator wants.
Even after disruption, new variants or copycat activity can appear because the underlying methods still work and the source code or techniques may circulate.
Another factor is cost. Criminals do not need every campaign to succeed at a high rate. They need it to succeed enough. If a botnet sends millions of emails and only a fraction convert into infections, extortion payments, or clipped transactions, the numbers can still make sense for the attackers.
That is the uncomfortable business logic behind Phorpiex botnet ransomware attack campaigns. The methods are cheap, the infrastructure can be reused, and the outcomes can vary. That makes Phorpiex less like a one-time threat and more like a criminal toolkit that keeps finding new chances to earn.
Who is Most at Risk?
The short answer is almost everyone who relies on email, file attachments, or digital payments. But the practical risk is higher for organizations with weak email filtering, users who regularly handle attachments, and teams without strong endpoint monitoring.
Recent ransomware advisories from CISA also show how ransomware operators broadly target organizations across critical sectors, which means industry alone is not a shield.
Small businesses may be especially exposed because they often sit in the awkward middle. They are valuable enough to extort, but not always protected by mature security teams.
They may also rely heavily on shared inboxes, downloaded invoices, and quick payment workflows. That is exactly the kind of environment where a phishing-led malware chain can slip through.
Individual users are not off the hook either. Sextortion messages prey on fear. Crypto clippers prey on routine. Ransomware preys on urgency. The common thread is human behavior under pressure. That is why any serious analysis of the Phorpiex botnet ransomware attack has to include not just malware mechanics, but user psychology too.
Technical Signals That Matter
Public reporting on Phorpiex has highlighted several recurring traits. Researchers have described phishing emails with document-themed lures, malicious shortcut files, PowerShell-based download activity, and follow-on payload delivery.
Older research also tied variants to peer-to-peer functionality and wallet-address replacement for crypto theft.
For security teams, this means detection cannot rely on one static indicator. The delivery layer may change, the payload may change, and the lure may change.
What tends to remain valuable is behavior-based monitoring. Suspicious shortcut execution, unusual PowerShell activity, unexpected outbound requests, and unauthorized clipboard manipulation should all raise concern.
That is one content gap many summary articles miss. The Phorpiex botnet ransomware attack is not just a malware family to block by name. It is a chain of behavior to interrupt. Defenders who focus only on threat labels may miss the more reliable signs unfolding right in front of them.
-20260403124454.webp)
What Users and Companies Should Do Now
The most useful advice is still the least glamorous. Patch systems. Harden email defenses. Block risky attachment types where practical. Restrict script execution where it is not needed. Train users to treat unexpected document lures with suspicion, especially compressed files and shortcut attachments. CISA also recommends tested backups, multi-factor authentication, and segmented recovery planning as part of ransomware readiness.
For crypto users, the fix is even simpler, though not always followed. Verify the wallet address before confirming a transfer. Better yet, compare the first and last characters through a trusted out-of-band method or use saved addresses only after independent review. One careless paste can be expensive.
If you are responding to a possible Phorpiex botnet ransomware attack, speed matters. Isolate the affected device. Preserve logs if possible. Reset exposed credentials.
Review email activity around the original lure. If cryptocurrency was involved, document the transaction details immediately. Every minute counts, but panic is the enemy. Calm, structured response beats frantic clicking every time.
Hoplon Insight Box
Hoplon Insight Box: What smart defenders should prioritize
- Treat suspicious shortcut files and script-driven downloads as high-priority alerts.
- Review email security policies for archive files, shortcut attachments, and document lures.
- Teach finance and operations staff to verify crypto wallet addresses before transfers.
- Keep offline or immutable backups and test recovery, not just backup creation.
- Assume mixed objectives in Phorpiex-related campaigns, including ransomware, fraud, and extortion.
- Build detections around behavior, not just malware names.
Final Takeaway
The Phorpiex botnet ransomware attack is not important because it is new. It is important because it is durable. It keeps resurfacing in forms that feel ordinary enough to be ignored and dangerous enough to hurt businesses and individuals who do ignore it.
That is the real lesson. The threat is not only the malware. It is the combination of old habits, trusted workflows, and small moments of inattention that attackers know how to exploit.
When a botnet can help spread ransomware, power sextortion campaigns, and quietly steal crypto through clipboard swaps, the smart response is not narrow.
It is layered, realistic, and immediate. The Phorpiex botnet ransomware attack deserves that level of attention, and probably more.
You can also read these important cybersecurity news articles on our website.
· Apple Update,
For more, please visit our homepage and follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well.
Was this article helpful?
React to this post and see the live totals.
Share this :