WhatsApp Security Alert Fake iOS App Spyware Hits 200 Users
Hoplon InfoSec
02 Apr, 2026
WhatsApp Security Alert Fake iOS App Spyware
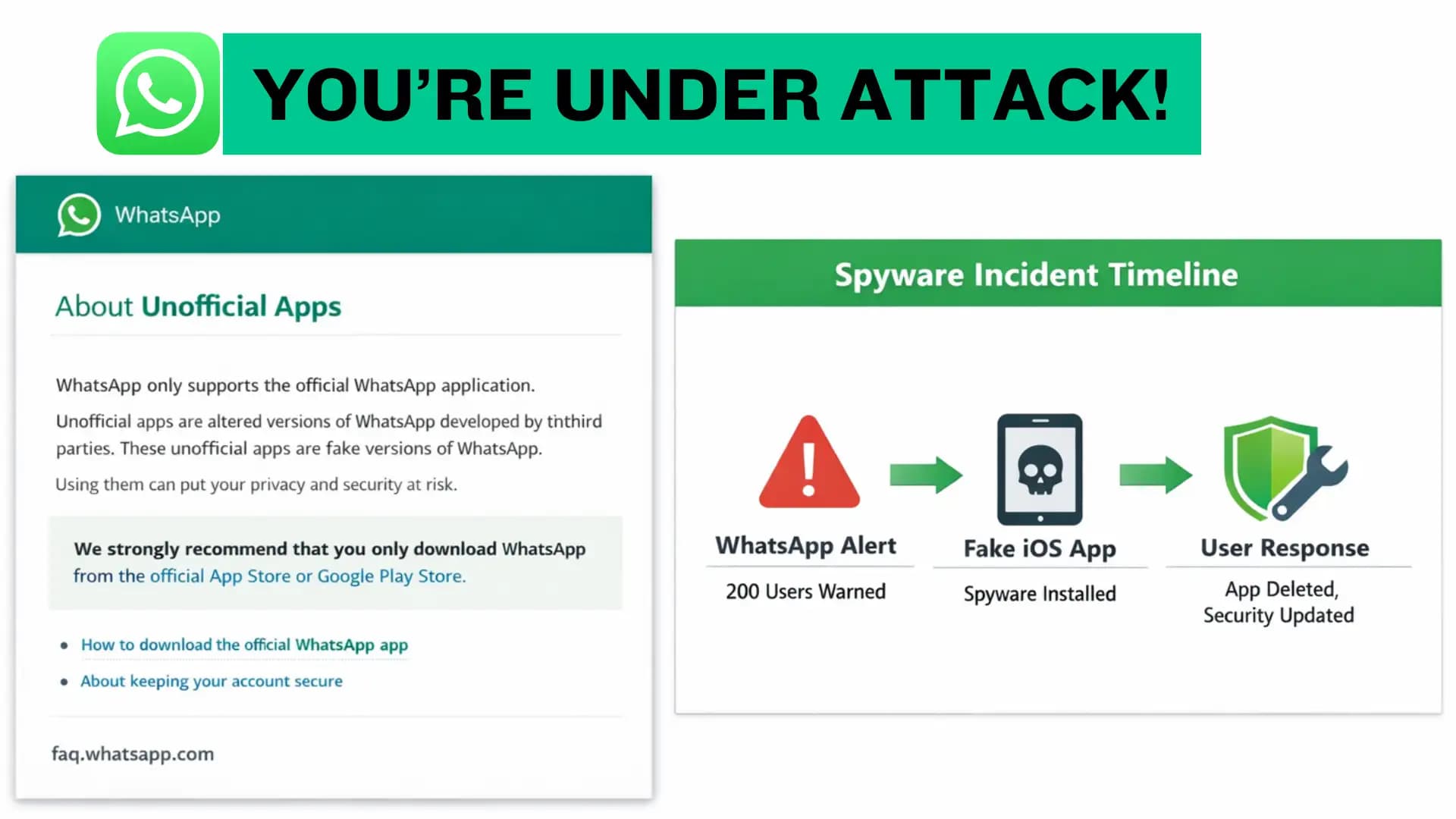
Was this a WhatsApp app problem or something bigger? On April 1, 2026, WhatsApp said about 200 users, mainly in Italy, were tricked into installing a fake version of the app that carried spyware. Reuters and TechCrunch both reported that WhatsApp linked the campaign to ASIGINT, a subsidiary of the Italian surveillance company SIO, while WhatsApp’s own help pages warn that unofficial apps are fake third-party apps and should not be trusted.
What makes this story important is that it was not a normal app bug. The public reporting points to deception, a counterfeit client, and spyware, not a named CVE or a traditional software vulnerability. In plain language, this is the kind of case where the attacker does not need to break the app first. They just need to fool the user first. That is why the WhatsApp security alert fake iOS app spyware story matters far beyond one country or one company.
What happened in this case
The core of the incident is simple. WhatsApp said around 200 people were alerted after they were believed to have downloaded a malicious unofficial client that impersonated WhatsApp. Reuters reported that the campaign was highly targeted and relied on deception to get victims to install software that mimicked WhatsApp, with the vast majority of targets in Italy. TechCrunch added that WhatsApp logged affected users out and told them to remove the fake app and install the official one.
That detail matters because it shows how spyware operations often work now. Attackers do not always need a flashy zero-day exploit. Sometimes the shortest path is social engineering, trust, and a believable fake. In this case, the danger sat inside an app that looked familiar enough to lower the victim’s guard. That is what makes the WhatsApp security alert fake iOS app spyware case feel so uncomfortable. It reminds users that a familiar logo can still hide a very different tool.
Why this case matters right now
There is also a wider pattern here. Reuters said this was the second time in 15 months that Meta publicly disrupted spyware activity in Italy, and TechCrunch noted that WhatsApp had previously notified around 90 users in early 2025 in a separate Paragon-related case. That earlier episode involved journalists and pro-immigration activists, according to TechCrunch, which shows how targeted these operations can be.
That history gives the current alert more weight. It is not just a one-off scare. It looks like part of a continuing surveillance pressure point in Italy, where spyware vendors, intelligence-linked customers, and public backlash have already collided before. In other words, the latest WhatsApp security alert fake iOS app spyware report is both a user safety issue and a signal about how persistent this market has become.

How the fake app trick worked
The public reporting suggests a classic social engineering play. A counterfeit app was presented as WhatsApp, and users were persuaded to install it outside normal trust paths. Reuters described the malicious software as impersonating WhatsApp, while TechCrunch said WhatsApp identified the app as a malicious unofficial client. WhatsApp’s own Help Center says unofficial apps or websites are fake WhatsApp apps developed by third parties, which is exactly why the warning is so direct.
That is the part many readers miss. They think spyware only shows up through a complicated hack. In reality, a convincing fake app can do the job just fine if the user is rushed, curious, or simply not expecting danger. A fake install route can be enough to hand over access, especially when the app is wrapped in a familiar name and a trusted icon. This is the practical lesson buried inside the WhatsApp security alert fake iOS app spyware case.
Who is accused of making it
Reuters reported that WhatsApp said the campaign was carried out by ASIGINT, a subsidiary of the northern Italy based company SIO. TechCrunch also said WhatsApp accused Italian spyware maker SIO of creating a fake version of its messaging app for iPhones. Reuters further reported that SIO describes itself as a provider of high-performance cyber intelligence solutions and says it works with law enforcement and intelligence agencies.
That does not mean every detail is publicly settled. Neither Reuters nor TechCrunch reported a detailed technical teardown of the spyware payload in this case, and the company and authorities did not immediately respond in the Reuters report. So the safest read is this: WhatsApp publicly named the company it believes is responsible, but the full technical chain has not been laid out in public reporting.
What users should do now
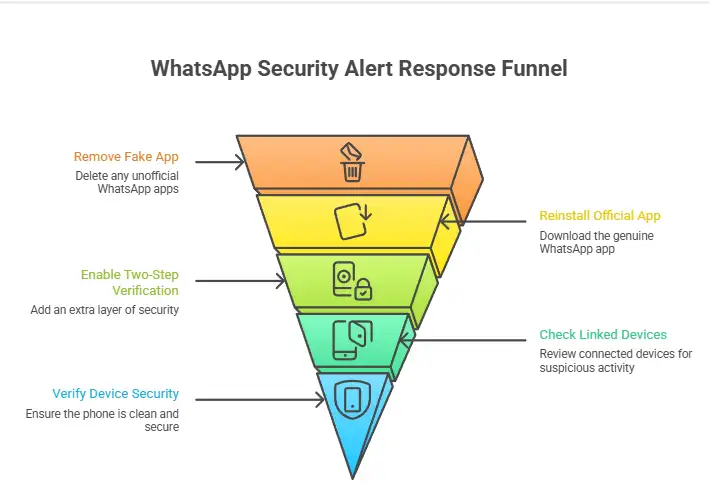
WhatsApp’s own guidance is the best place to start. The Help Center says unofficial apps are fake apps made by third parties, and its account security tips recommend enabling two-step verification, turning on chat lock, and using app lock. The company also told affected users in this case to remove the fake app and download the official WhatsApp app.
For a regular user, the response should be calm and direct. Remove any app that did not come from the official route. Reinstall only the official WhatsApp app. Turn on two-step verification. Check linked devices. And, if the phone acted strangely after the install, treat the device as potentially exposed until it is cleaned and verified. That is the simplest safe response to this WhatsApp security alert fake iOS app spyware warning.
What most short news posts leave out
A lot of quick coverage stops at the headline. That is the easy part. The missing piece is the behavior pattern. This was not just a fake app story. It was a social engineering story, a surveillance story, and a trust story all at once. Reuters emphasized the deception angle, TechCrunch highlighted the official warning and user logouts, and WhatsApp’s help pages explain why unofficial apps are risky in the first place.
Another gap is the user guidance gap. People often ask, “What now?” The official answer is short but useful. Use the official app, enable two-step verification, and do not trust third-party clones. That sounds obvious, but obvious advice is often the advice people ignore until the day it becomes urgent. The WhatsApp security alert fake iOS app spyware report is exactly the kind of moment when the simple advice becomes the important advice.
Mini risk snapshot
The risk was not a random app glitch. It was a fake WhatsApp client used to deliver spyware. The likely targets were around 200 users, mostly in Italy. The company named by WhatsApp was ASIGINT, linked to SIO. The public reports do not cite a CVE, which supports the idea that this was a deceptive installation campaign rather than a disclosed software flaw.
That distinction matters because it changes how you defend against it. You cannot patch away bad judgment, but you can reduce the chance of falling for a fake app. That means checking the source, checking the publisher, and treating unofficial installs as a warning sign. In this case, the label on the icon mattered less than the path used to install it.
Research note
A useful line from Citizen Lab’s phishing research is that attackers used methods designed to “bolster the social engineering aspect” of fake login pages. That phrase is old, but the lesson is still current. The tools change, the pressure changes, and the target changes, yet the trick is often the same. Make the fake feel normal enough for one rushed tap.
Hoplon Insight Box
The safest response to a story like this is a short checklist.
First, trust the official app path only. WhatsApp’s Help Center says unofficial apps are fake third-party apps, so a clone should never be treated as harmless. Second, turn on two-step verification and app lock. Third, review linked devices and remove anything you do not recognize. Fourth, if you downloaded a suspicious clone, reinstall WhatsApp from the official source and watch for unusual account activity.
For teams, the bigger lesson is simple. Security awareness is not just a corporate slideshow. It is a habit. When a platform like WhatsApp issues a warning, the safest move is to slow down, verify the source, and assume the fake app was built to look boring, familiar, and trustworthy. That is why the WhatsApp security alert fake iOS app spyware case deserves attention well beyond the original 200 users.
FAQ
1. Is the fake WhatsApp iOS app still a threat?
The public reports show that the campaign was serious enough for WhatsApp to
alert users and push removals, but they do not provide a live threat status
page. The safe assumption is that fake app lures can reappear in new forms, so
users should keep using the official app only.
2. How do I know whether my WhatsApp app is official?
WhatsApp says unofficial apps are fake apps developed by third parties. The
safest method is to install WhatsApp only from the official app source and
avoid side-loaded or cloned versions.
3. What should I do if I installed a suspicious WhatsApp clone?
Remove it, install the official app again, enable two-step verification, and
review linked devices. WhatsApp’s help pages support all three of those steps.
4. Was a CVE involved in this incident?
I could not verify any public CVE tied to this case. The reporting I checked
focuses on a fake app and spyware distribution campaign, not a disclosed
software vulnerability.
You can also read these important cybersecurity news articles on our website.
· Apple Update,
· TikTok Warning
· Apple OS update
For more, please visit our homepage and follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well.
Was this article helpful?
React to this post and see the live totals.
Share this :