KB5074105 Storage Admin Access in Windows 11: Full Guide

Hoplon InfoSec
02 Feb, 2026
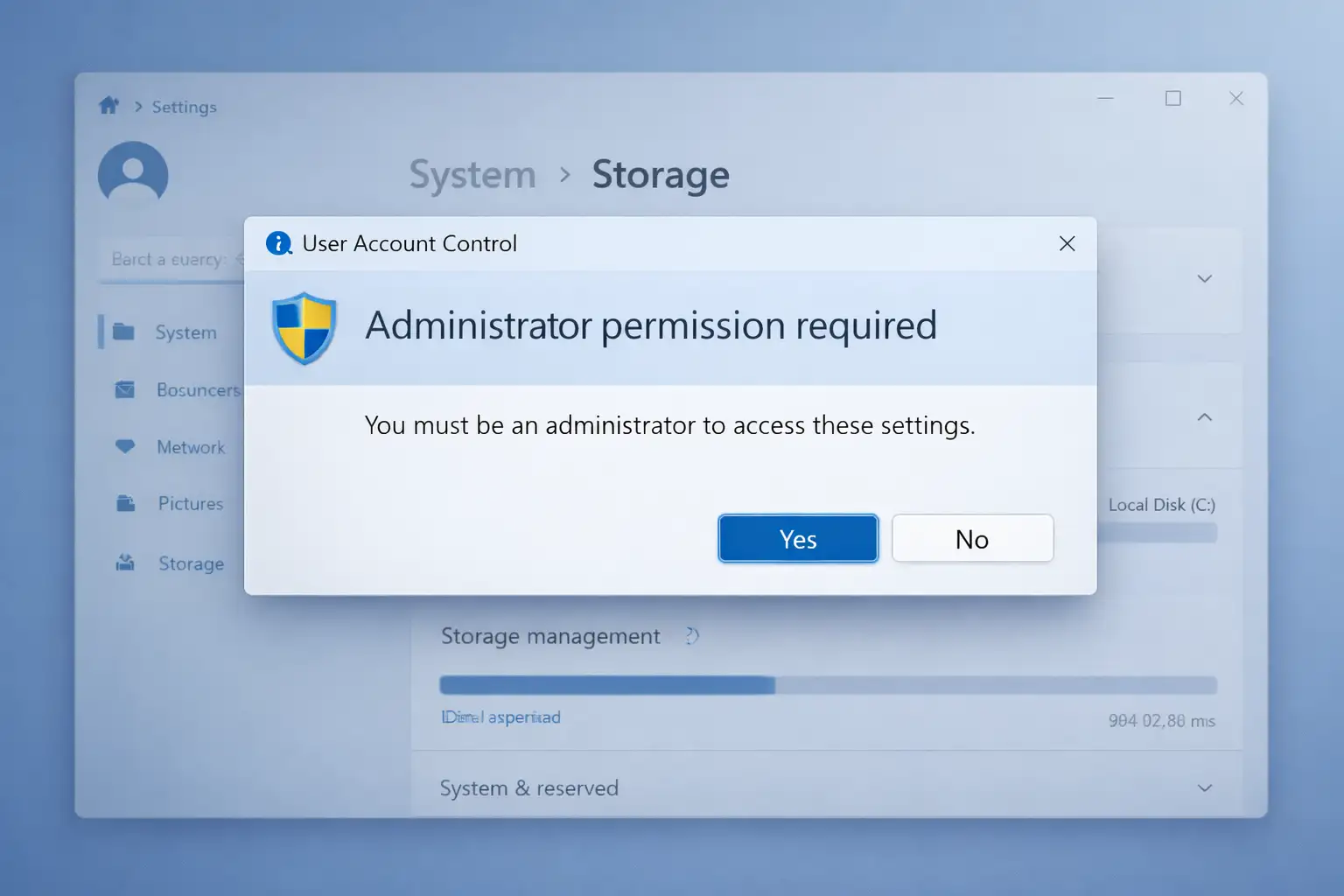
Windows 11 KB5074105 introduced a new admin access requirement for Storage settings. After installing the January 2026 preview update, users may now see a User Account Control (UAC) prompt when opening Settings > System > Storage.
Microsoft says the change is intended to help ensure that only authorized Windows users can access system files. This article explains what the KB5074105 Storage admin access change does, why it matters, who is affected, and how to deal with it.
What Is Windows 11 KB5074105?
KB5074105 is a non-security preview update released on January 29, 2026 for Windows 11 version 24H2 and 25H2. While the update includes general fixes and reliability improvements, one of the most discussed changes is a new admin access prompt for the Storage settings page.
This is the change most users are referring to when they search for “Windows 11 KB5074105 storage admin access.
Why Does KB5074105 Require Admin Access for Storage Settings?
Microsoft added a new protection layer in KB5074105 so that opening Settings > System > Storage now triggers a User Account Control (UAC) prompt. According to Microsoft’s release notes, the goal is to help ensure that only authorized Windows users can access system files. In practice, this means Storage settings is no longer treated as a simple informational page for all users. Instead, Windows now requires elevated approval before showing system-sensitive storage data
What Happened and What the Update Does
Earlier in February 2026, Microsoft shipped the KB5074105 Windows 11 preview cumulative update for versions 24H2 and 25H2 that includes a stealth security enhancement. When trying to open certain system-related interfaces, like detailed storage settings, it triggers an administrative prompt via User Account Control (UAC) before entering.
If the account lacks admin rights, users are blocked entirely. This is a form of access hardening that goes beyond basic file permissions and enforces consent before even viewing structured system data that could otherwise be exploited by someone with physical or remote access to the PC.
This feature is rolling out in the “C-release” optional preview phase ahead of broader deployment in the mandatory Patch Tuesday updates. Businesses and power users should test the feature before it is made available to everyone else so that workflows that rely on seeing system files are not interrupted.
This change is part of a bigger security philosophy for Windows 11 that focuses on giving users the least amount of access and making it harder for attackers to get in. Windows 11 already has security features like Microsoft Defender, controlled folder access, and virtualization-based protections to keep devices safe.
Is the KB5074105 Storage Admin Access Change a Bug or an Intentional Feature?
The available reporting and Microsoft’s own wording suggest this is an intentional security change, not just a random bug.
Microsoft specifically added release-note language stating that Windows now shows a UAC prompt when opening Storage settings to limit system file access to authorized users. Multiple Windows-focused publications also reported that the behavior is by design rather than an accidental regression.
Which Windows 11 Versions Are Affected?
Microsoft lists Windows 11 version 24H2 and 25H2 as the versions covered by KB5074105. The update was first released as an optional preview update, which means some users saw the new Storage admin access behavior before it reached a wider audience through later servicing updates
Does KB5074105 Affect Temporary Files Cleanup?
Some third-party reporting noted a side effect after KB5074105: parts of the Temporary files cleanup interface may not show all cleanup categories in the same way as before, including cases involving Windows Update files.
This appears to be related to the new elevated-access behavior around Storage settings. Because this specific side effect is discussed mainly in third-party coverage rather than Microsoft’s core release note, it should be presented carefully as a reported impact rather than a formally documented Microsoft guarantee.
How the New Windows 11 Security Feature Works at the System Level to Restrict Unauthorized Access
A look at how the new security feature in Windows 11 works at the system level
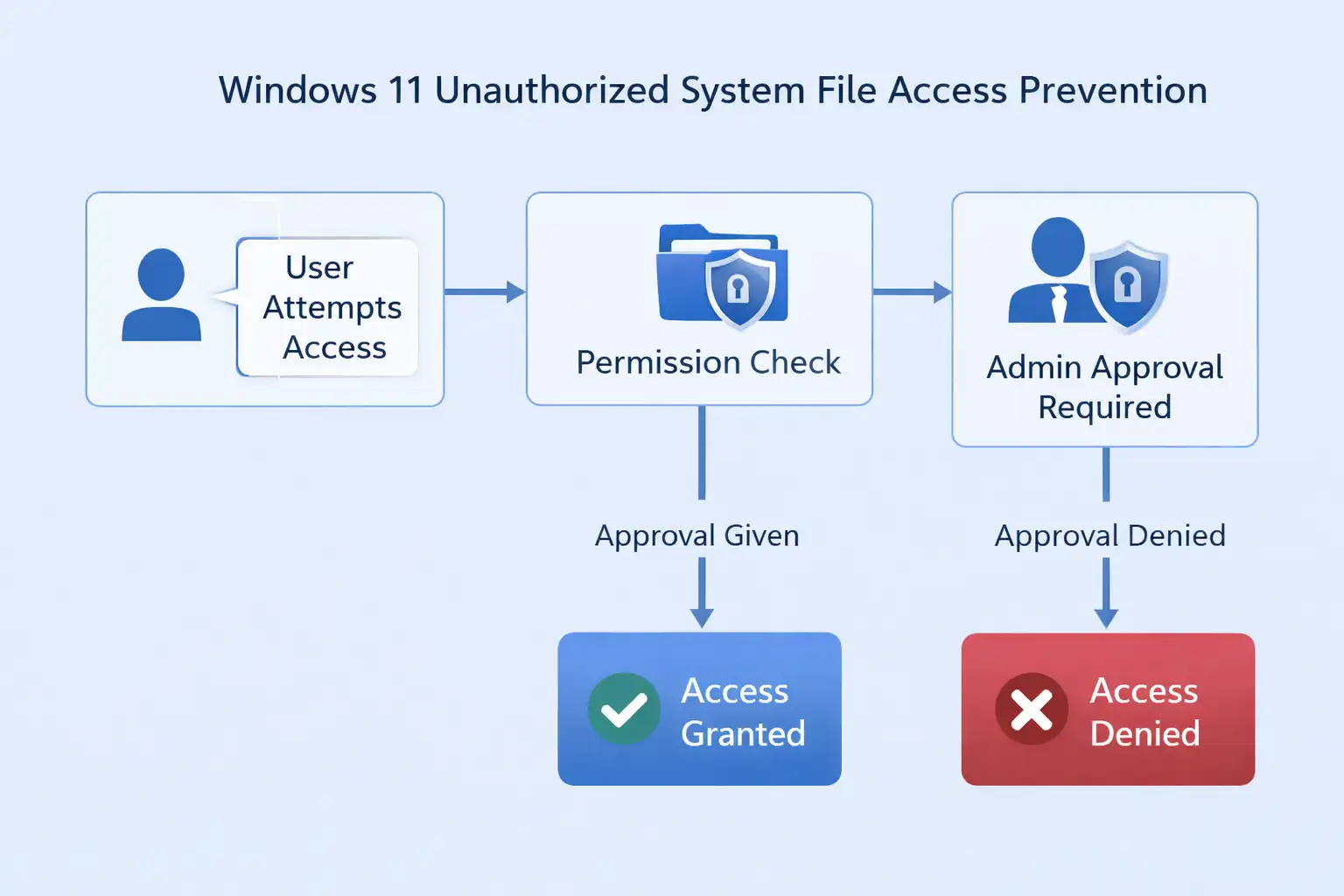
With this new Windows 11 security feature, access is checked at the interface level as well. This is different from the old way of checking file permissions, which only uses NTFS access control lists (ACLs). When a user tries to open certain system-sensitive areas, like the detailed Storage breakdowns in Settings, the operating system now checks to see if they are elevated before showing protected data.
Behind the scenes, these things happen:
Windows does a User Account Control (UAC) check when a regular user account tries to access a secure system port. The system checks more than just whether files can be read. It also checks to see if the current session has a higher administrative access token. This is what the system does before it shows structured data about system files: it stops the request if the session doesn't have enough rights.
This is important since:
• NTFS rights decide who can see files.
• When you raise UAC, the session's permission level is set.
• The new feature needs to be given permission before it can show organized system data.
Or to put it another way, the security starts before the Settings screen shows detailed system details. Users who aren't administrators can't see system-reserved storage, temporary system files, or protected operating system structures without first getting permission from an administrator. Malware that runs under normal accounts may also not be able to see these areas.
Windows 11 is creating a layered defense model by combining enforcement at the interface level with file rights that are already in place. In other words, it doesn't depend on just one way to control entry.
Why Microsoft Is Tightening System File Access
System files and low-level settings in any operating system carry a lot of risk. In the past, users and malware could use built-in tools and scripts to get to the internals of a system, which could have exposed sensitive data structures or allowed unwanted changes.
Windows has had User Account Control for a while, but Microsoft has been working on how and when it works to make sure that administrative consent is given.
UAC limitations were historically circumvented by determined threats using token manipulation or abusing elevated sessions.
The latest Windows 11 security feature builds on this by enforcing administrative obstacles even for standard file browsing beyond classic user permission models. The goal is to make unauthorized access to critical system information much harder and to ensure that users with legitimate administrator rights explicitly confirm actions that touch protected system resources.
How to Fix or Work Around the Windows 11 KB5074105 Storage Admin Access Prompt
If you see the new Storage admin access prompt after installing KB5074105, the first step is to confirm whether your Windows account has administrator rights. If it does, approve the UAC prompt and continue.
If you are using a standard account, you may need an administrator to authorize access. On managed business devices, the prompt may be part of an intentional least-privilege policy rather than a system error. Users should also check Settings > Windows Update > Update history to confirm whether KB5074105 is installed
How This Affects Everyday Users
For typical home users, the impact will be subtle. Most people never navigate deep into system folders or storage breakdowns in the first place. If you are a standard user account without admin rights, you will now see a UAC prompt or be blocked when trying to access these areas.
This means for people who share spaces like libraries, schools, or even homes with more than one person:
• Windows 11 will stop accounts with fewer privileges from accidentally or purposefully getting into the system's inner workings.
• IT professionals will have a better idea of who can control access to core system files.
• Malware that runs under standard accounts without elevation will find it harder to collect system information or alter system structures.
In other words, security boundaries are being raised to align with modern threat tactics without requiring additional third-party security tools.
Enterprise Impact of the Windows 11 Security Update on Domain PCs and IT Administrators
What this means for business environments, domain PCs, and IT managers
This update doesn't change much for people who use it at home, but it does change a lot for businesses and sites that are already linked.
A lot of people who work for businesses use standard user accounts, and Active Directory or Microsoft Entra ID tightly controls who has management rights. In the past, structured system storage information could be seen by anyone, not just administrators. That's harder to see now that this has been fixed.
There are several ways this change is good for IT managers:
• Lessened the chance that hacked user accounts could be used for internal spying
• More strict regulation of access models that give the least amount of power
• A thicker line between the roles of operations and administration
• More safety for shared computers or computers that look like kiosks
PCs in the same domain should behave similarly unless certain management rules tell them otherwise. Users of Microsoft Intune or Endpoint Manager may want to check to see if their inventory software, automation scripts, or diagnostic tools need to view system storage data that isn't set to "high."
Before this update is sent to everyone, administrators should try it in controlled settings. This is especially important in businesses where scripts change Windows Settings or system storage parts.
Overall, this fits with Microsoft's strategy for workplace security, which is to limit access to system internals that isn't needed while still letting administrators do their jobs in a controlled way.
Example: Storage Settings Prompt
Before the update, anyone who could log into a Windows 11 session could open the Settings app, navigate to System → Storage, and see detailed file breakdowns, including system-reserved or temporary files. After the update, attempting the same action brings up an administrator approval dialog if the account is not elevated. Without admin credentials, Windows will refuse to continue.
This is not just a permission check on a file system level but a security checkpoint, like what IT administrators have long asked for to curb unauthorized system exploration in business or sensitive environments.
What Happens When You Open Storage Settings After KB5074105?
After installing KB5074105, opening Settings > System > Storage can trigger a UAC approval request. If the user has administrator rights, they can approve the prompt and continue. If the user does not have admin rights, access may be blocked unless an administrator approves the request. For home users this may feel like a small workflow change, but for shared PCs, school devices, or business-managed systems, it is a more meaningful security boundary.
How This Fits Into Windows 11’s Larger Security Ecosystem
This Windows 11 new security feature is one of many steps Microsoft has taken to harden the operating system. Windows 11 already has built-in protections like these:
Controlled Folder Access protects user folders from malware and writes that aren't allowed.
Microsoft Defender Antivirus and Smart App Control check apps before they run.
Hardware-assisted security through TPM, secure boot, and virtualization-based security to isolate kernel and boot processes.
This latest block on unauthorized system file access is part of the same direction: protect the OS at every layer from unauthorized exploration or manipulation while preserving legitimate administrative workflows.
-20260202125954.webp)
What Windows Users and Administrators Should Do
Because this feature is currently in preview, administrators should:
Test the impact on enterprise images before wide deployment.
Look at automated scripts or tools that might need unrestricted access to settings or storage.
Teach regular users about the new UAC prompts they might see.
Home users don't need to do anything else but keep Windows up to date to get the latest security updates.
Troubleshooting Windows 11 Storage Access Blocked by the New Admin Security Prompt
Here's what to do if you can't get to the storage settings.
Why might you not be able to open the detailed Storage settings? Here are some ideas on how to fix the issue.
First, make sure you have the right kind of account:
First, go to Settings and click on Accounts. Then, click on Your Info.
2. Check to see if you are an Administrator or a Standard User in your account.
If you are using a standard account, you will need administrator rights to keep going. You may:
• Run Settings as an administrator if you can.
• Use an account that has management rights to log in.
• In managed settings, get permission from an admin.
If you are already a supervisor and are still having issues, look at these:
• If you've changed how User Account Control works.
• If the options for Group Policy make it hard to get to some places.
• If the preview update caused any issues that weren't planned for.
You can also go to Settings, then Windows Update, and then Update History to see if KB5074105 is in your build of Windows.
If you work for a business, talk to your IT staff because policies may make it hard to get to some parts of the system on purpose.
Companies may delay sample updates for a while if a new feature makes work more difficult until it has been tested to make sure it works with other programs.
Most of the time, the prompt works as it should. It only needs clear permission from the people in charge before protected system-level storage information can be seen.
The Future of Windows System Security
This trend shows that Microsoft will keep making the line between standard and elevated privileges clearer. Future updates may require prompts in other sensitive configuration areas besides storage, or they may change how people can access common system tools.
Security in 2026 and beyond is not only about blocking known malware. It is also about reducing the ability of any unauthorized process or unauthorized account to glean deep system details or alter the OS without explicit user consent.
Frequently Asked Questions
Why does Windows 11 block access to system files now?
Because Microsoft has added a protective check in the latest preview update to enforce consent before allowing access to sensitive system file areas, reducing unauthorized interaction.
Will I still be able to access Storage settings if I am an admin
Yes. Admin accounts will be asked to approve access before they can continue.
No, this does not change file permissions in Windows. This security feature adds another layer of UAC checks before checking permissions.
Can this feature be disabled?
Since it is part of a preview update, it may be optional until it is included in a mandatory Patch Tuesday release.
Conclusion
This new feature in Windows 11 is another step in the right direction for security. It stops people who shouldn't be able to access system file areas of the operating system. Users get better protection against abuse, and administrators get clearer limits on what privileged operations can and can't do.
It is a sign that Windows security is increasingly proactive and that visibility into system internals is being intentionally guarded to match modern threats.
Read more related blogs:
Author:By Hoplon Cybersecurity Research Team
Publish Date: February 2, 2026
Last Updated: April 13, 2026
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :