Cloud Security Risks: Europa Breach Every Business Must Use

Hoplon InfoSec
30 Mar, 2026
What does the European Commission data breach show about cloud security risks today?
What does the European Commission data breachshow about the risks of cloud security today, and why should businesses rethink how they use digital infrastructure?
A confirmed breach of the Europa.eu platform shows how attackers can use cloud environments to get to a lot of private information. It shows that threats are moving away from traditional system attacks and toward cloud-based ones, which forces businesses to use better identity protection and monitoring methods.
Not too long ago, most companies were mostly concerned with keeping their own networks safe. Everything has changed now that people are using cloud services.
In this case, the attackers went after a cloud-based environment instead of systems inside the company. The outcome is clear. Sensitive data was accessed, but the main systems stayed safe.
This event is important because it shows how big companies use cloud platforms. And even more importantly, how quickly attackers are changing.
Official reports say that the breach involved data taken from websites that were hosted on the European Commission's infrastructure.
What Went Wrong in the Data Breach at the European Commission?
The European Commission said that hackers attacked its Europa.eu platform, where they got to data stored in the cloud without affecting the systems inside.
The attack was connected to a group that is known for stealing data. They are said to have gotten into at least one cloud account that is connected to the Commission's web infrastructure.
The size is what stands out here. Reports say that hundreds of gigabytes of data may have been accessed before steps were taken to stop it.
The commission interestingly confirmed that:
- Internal systems were not affected
- The attack only affected certain web services
- Steps were taken right away to stop more access
That difference is important. It shows that there is a difference between systems that face the cloud and networks that are inside the company.
A lot of businesses use this layered method these days.
Why This Event is More Important Than It Seems
The breach shows a growing trend in which attackers target cloud platforms instead of traditional infrastructure.
Understanding and Insight
More and more businesses have been moving their operations to the cloud over the past few years. It is quicker, more flexible, and cheaper. But it also makes the attack surface bigger.
In this case, the attackers did not get into the main systems. Instead, they went after services that could be accessed from the outside.
That's a small but important change.
And if you think about it, a lot of businesses today use setups that are similar. Websites, APIs, and cloud storage. Everyone is connected in some way.
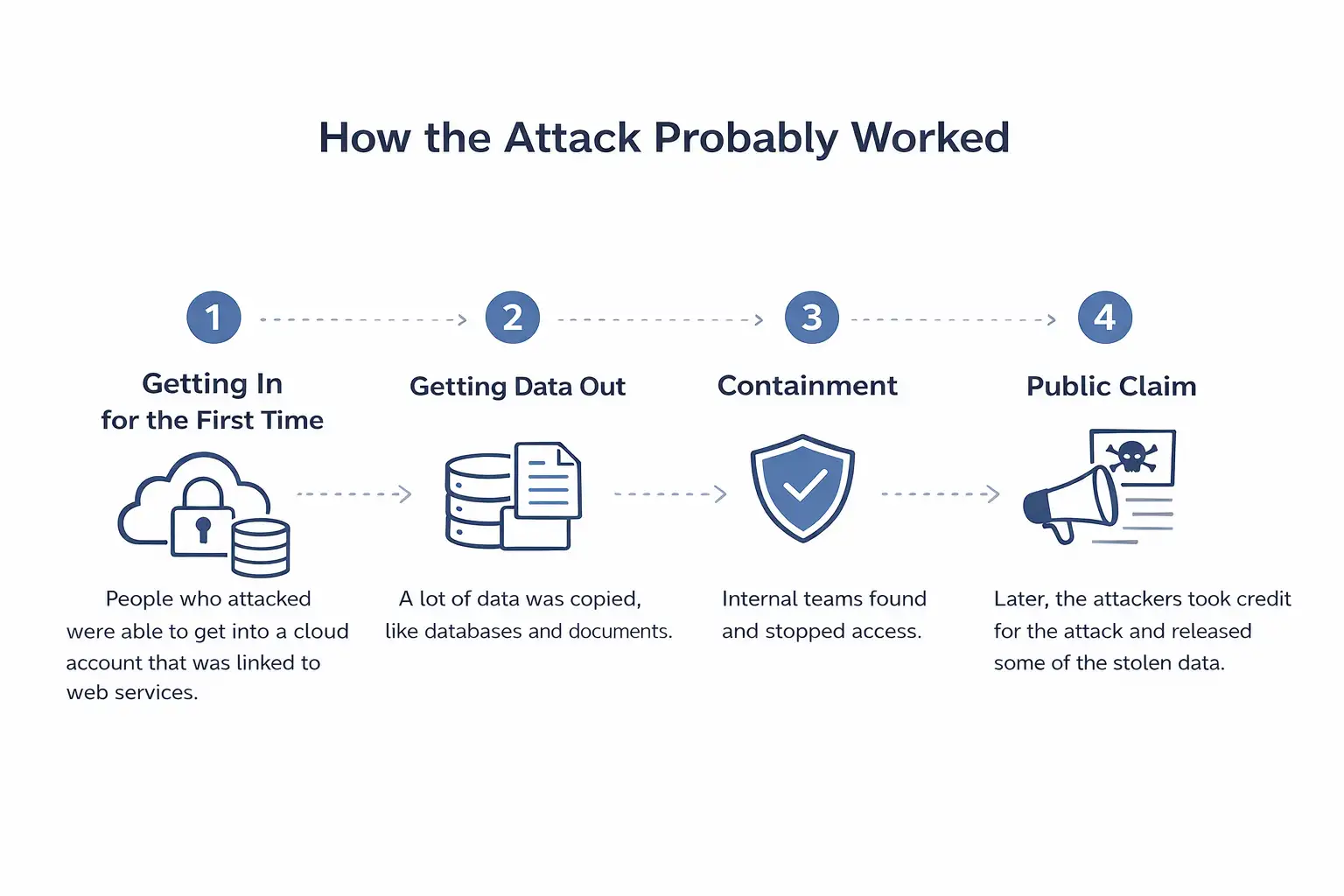
How the Attack Probably Worked
It looks like the attackers got into cloud accounts, stole data that was stored there, and tried to use it to blackmail people.
A Breakdown of Steps
- Getting In for the First Time
People who attacked were able to get into a cloud account that was linked to web services. - Getting Data Out
A lot of data was copied, like databases and documents. - Containment
Internal teams found and stopped access. - Public Claim
Later, the attackers took credit for the attack and released some of the stolen data.
This sequence fits with a lot of modern cyber events. Quick access. Quick extraction. Pressure from the public.
Before and After Cloud Security Awareness
Before things like this happened, a lot of businesses were mostly focused on:
- Firewalls for networks
- Protection at the endpoint
- Monitoring from within
After seeing breaches like this, priorities are changing to the following:
- Control of identity and access
- Checking the settings of the cloud
- Finding anomalies in real time
I've seen this happen in businesses before. Teams that used to ignore cloud logs are now looking at them every day.
Who is Affected by This Kind of Breach?
Many people, such as institutions, employees, and users who use the platform, may be affected.
Breakdown
- Government Organizations
They are at risk of damaging their reputation and their business. - Employees
Some information about employees may have been made public. - Users and Partners
Anyone who uses the affected systems could be affected in some way.
Even if core systems are safe, just exposing data can have long-term effects.
What is Good and Bad About the Current Response?
Good Things
- Quick containment stopped more data loss
- The systems inside stayed safe
- An ongoing investigation makes sure that everything is clear
Restrictions
- The exact method of attack is still unknown
- The full effect is still being looked into
- Risks of cloud exposure are still a problem
There's also a bigger worry. A lot of groups might have the same weaknesses, but they haven't found them yet.

What Companies Need to Do Now
Companies need to improve their cloud security practices, with a focus on access control, monitoring, and responding to incidents.
Real Steps
- Look over how you use cloud accounts and permissions
- Use two or more forms of authentication for all services
- Keep an eye on strange activity as it happens
- Check your cloud settings on a regular basis
Locking your house is a good way to think about it. It's not just the door in front of you. Every window is important.
Questions That Are Often Asked
1. Did the European Commission's internal system get hacked?
No. Official statements say that internal systems were not affected.
2. What kind of data was accessed?
It was said that data from web platforms, like databases and documents, was stolen.
3. How did the attackers get in?
There has been no official word on how it was done.
4. Is this part of a bigger trend?
Yes. A lot of recent attacks have been on identity systems and cloud services.
A Quiet Change in the Reality of Cybersecurity
This event doesn't just show a breach. It shows how the kinds of cyber threats are changing.
Organizations don't just protect networks anymore. They protect identities, cloud environments, and data streams.
And if you're in charge of digital infrastructure, now is a good time to stop and think about how you use cloud systems.
Key Takeaway
Security is no longer optional for businesses that use cloud platforms. It goes on and on.
Suggestion
Begin with access control. Most of the time, that's where the problems start.
Author
This article was written by an analyst who focuses on cybersecurity and has worked on cloud infrastructure risk and enterprise security strategy.
You can also read these important cybersecurity news articles on our website.
· Apple Update,
For more, please visit our homepage and follow us on X (Twitter) and LinkedIn for more cybersecurity news and updates. Stay connected on YouTube, Facebook, and Instagram as well.
Was this article helpful?
React to this post and see the live totals.
Share this :