TA446 DarkSword iOS Exploit Exposed: iPhone Risk Alert

Hoplon InfoSec
29 Mar, 2026
Are iPhones still safe in 2026?
After reports came out on March 26, 2026, about a targeted campaign using the TA446 DarkSword iOS exploit, many security teams began to ask this question. Proofpoint says that a Russian-linked threat group used a newly leaked iOS exploit kit to send carefully crafted phishing emails to high-value people.
This isn't just another phishing attempt. It shows a change. A well-known group of spies is now using a modular exploit kit made just for iOS devices, which was thought to be hard and uncommon for a long time.
This is important if you work in IT, cybersecurity, or even policy research. I'll explain what happened, how this exploit works, why it matters, and what you should do about it in this guide.
What is the TA446 DarkSword iOS Exploit? Complete Breakdown
What is the TA446 DarkSword iOS hack? The TA446 DarkSword iOS exploit is a targeted attack campaign in which the threat actor TA446 uses the DarkSword exploit kit to hack into iOS devices. Let's make that easier to understand.
The Russian Federal Security Service is linked to the state-linked threat group TA446, which is also known as Callisto or Star Blizzard. They are known for spear phishing campaigns that go after politicians, researchers, and groups that work with sensitive information.
DarkSword, on the other hand, is an exploit kit that targets weaknesses in Apple's iOS ecosystem. Exploit kits are different from regular malware in that they usually work through links or browsers without the user having to install anything.
The combination is what makes this
campaign stand out:
• An actor from a nation-state
• An exploit kit that has been leaked and is ready to use
• A move toward targeting mobile devices
Before, TA446 was mostly about stealing credentials. They have now moved into direct device exploitation with DarkSword.
TA446 iOS Exploit Campaign Explained: What Happened in This Attack
What went down in this campaign? The campaign started with spear-phishing emails that looked like invitations from the Atlantic Council. These emails looked real, were well-written, and were sent to specific people.
One of the known targets was a Russian opposition figure, which shows how serious this operation was.
This is how the attack went down:
• Emails were sent from accounts that had been hacked.
• The message had a link that looked like an invitation to a discussion.
• When you clicked on the link on an iPhone, it sent you to a different page.
• That redirect took you to the DarkSword exploit chain.
If the system found a device that wasn't an iPhone or a security sandbox, it sent a harmless PDF instead. This shows that they are very good at targeting and getting away.
Malware like GHOSTBLADE or MAYBEROBOT could be used at the end of the chain to get sensitive information.
How the TA446 DarkSword iOS Exploit Works: Step-by-Step Attack Chain
You can see how dangerous the TA446 DarkSword iOS exploit is by learning how it works. This is a multi-stage attack at a high level.
- Getting in through spear phishing
The attacker sends an email that looks real. It doesn't look bad at all. It often copies trusted organizations, though. The goal is easy. Make the user click. - Fingerprinting devices
After you click the link, the server checks the following:
• Is this an iPhone?
• What version of iOS is running?
• Is it a real person or a security sandbox?
Nothing happens if it doesn't match the target profile.
- Take advantage of delivery
If certain conditions are met, the exploit kit sends the following:
• Exploit that works in a browser
• Payload for remote code execution
• Bypass of the Pointer Authentication Code
This is where the real harm starts.
- Running the payload
After that, the system can install the following:
• Data miner for GHOSTBLADE
• MAYBEROBOT backdoor
These tools let hackers get to files, passwords, and messages.

Why the TA446 DarkSword iOS Exploit Matters for Cybersecurity in 2026
The TA446 DarkSword iOS exploit changes something that has been true in cybersecurity for a long time.
A lot of people thought that iPhones were pretty safe from being used on a large scale. This campaign goes against that idea.
This is why it matters:
• Nation-state actors are now actively going after iOS
• More and more people can get exploit kits.
• Attacks are no longer just on desktops
The leak of DarkSword itself is another big worry. Reports say that a version showed up on GitHub, which could let attackers with less skill use more advanced methods.
That has a ripple effect.
What used to be limited to high-level threat actors can now spread more widely.
Real-World Example of a TA446 iOS Spear Phishing Attack
Think about this.
You work as a policy analyst at a think tank. You get an email asking you to join a high-level meeting. The person who sent it seems real. The subject fits with what you do.
You click.
Nothing out of the ordinary happens. A PDF might open. You go on.
But in the background, someone has already hacked your iPhone.
Now:
• You can get to your emails
• Your iCloud information could be public.
• Someone is listening in on your conversations.
That's how sneaky we are.
Impact Analysis: Who is Targeted by the TA446 DarkSword iOS Exploit
This campaign is not by chance. It is very focused.
Based on what was seen, the targets
were:
• Groups that work for the government
• Groups that think
• Schools
• Banks and other financial institutions
• Law firms
But there's a catch.
Researchers said that the targeting was broader than usual. That means the attackers might be testing a wider deployment.
This raises the level of risk beyond just well-known people.
Common Misconceptions About iOS Security and Mobile Threats
Things People Get Wrong About iOS Security
Let's get rid of some false ideas.
A lot of people still think that iPhones can't get malware. That's not right. They are safer, but not completely safe.
Another wrong idea is that only high-ranking officials are at risk. That was mostly true before, but tools like DarkSword might change that.
Some people also think that phishing only takes passwords. Phishing is just the first step in modern attacks like this that can take over a whole device.
Indicators of Compromise (IoCs) for TA446 DarkSword iOS Exploit Attacks
There are a few signs to look out
for, even though it's hard to find them:
• Alerts for unexpected logins
• Weird redirects in the browser
• Strange things happening in the background
• Changes to the configuration that are not known
Security teams should also keep an eye on domains that are connected to exploit infrastructure, like the ones that are mentioned in malware samples.
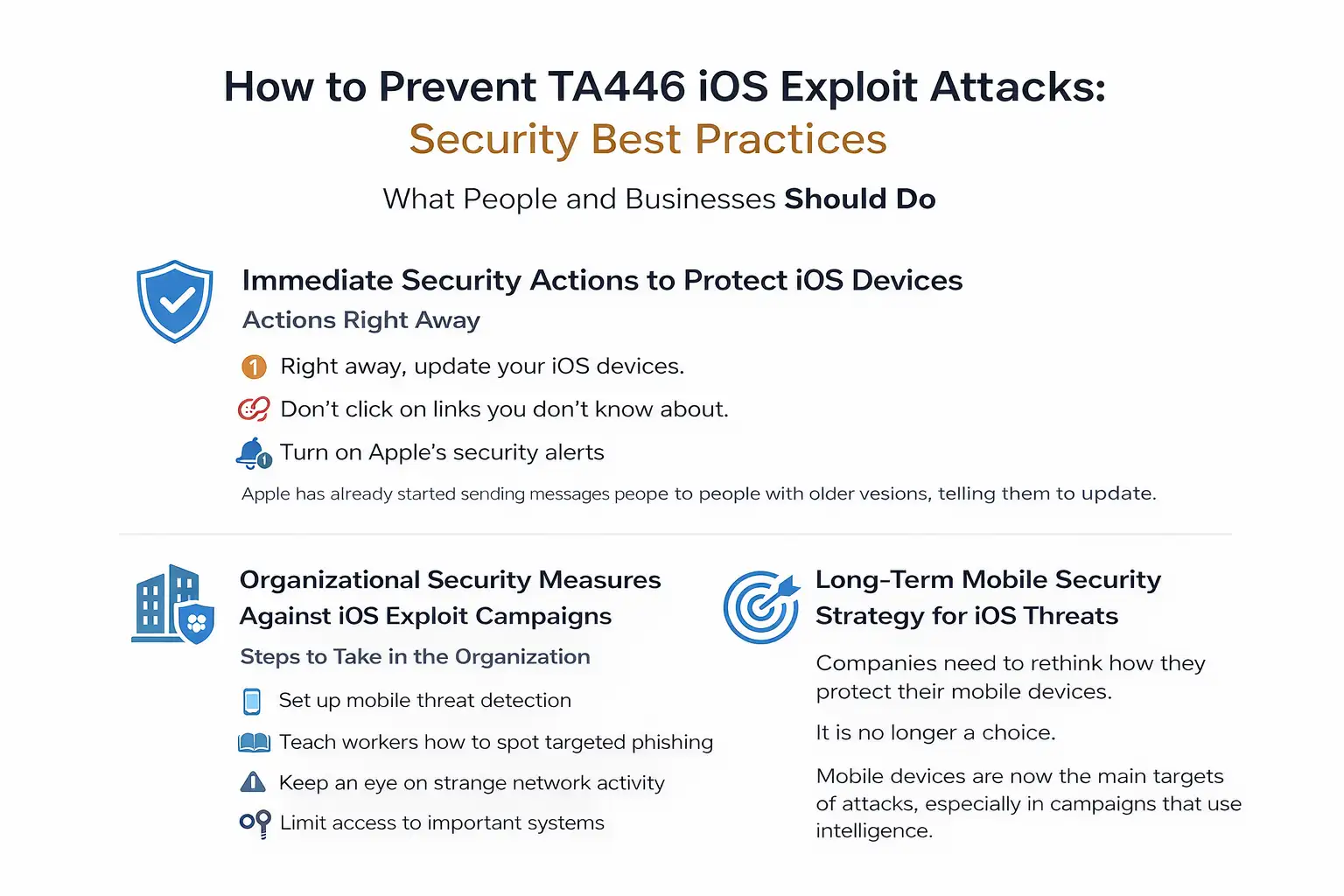
How to Prevent TA446 iOS Exploit Attacks: Security Best Practices
What People and Businesses Should Do
This is where things start to work.
Immediate Security Actions to Protect iOS Devices
Actions Right Away
• Right away, update your iOS
devices.
• Don't click on links you don't know about.
• Turn on Apple's security alerts
Apple has already started sending messages to people with older versions, telling them to update.
Organizational Security Measures Against iOS Exploit Campaigns
Steps to Take in the Organization
• Set up mobile threat detection
• Teach workers how to spot targeted phishing
• Keep an eye on strange network activity
• Limit access to important systems
Long-Term Mobile Security Strategy for iOS Threats
Plan for the Long Term
Companies need to rethink how they protect their mobile devices.
It is no longer a choice.
Mobile devices are now the main targets of attacks, especially in campaigns that use intelligence.
Key Cybersecurity Lessons from the TA446 DarkSword iOS Campaign
The TA446 DarkSword iOS exploit shows a bigger change.
Cyber threats are getting
• More focused
• More parts that fit together
• Easier to get to
The line between tools used by nation-states and malware that is sold as a commodity is starting to blur.
That's a big worry.
Once advanced tools are widely available, attacks can happen much more often and on a much larger scale.
Expert Security Recommendations for iOS Threat Protection
Advice from an Expert:
• Don't treat mobile devices as
secondary endpoints; treat them as critical ones.
• Use tools to find mobile endpoints
• Check the settings on your devices often.
• Think that phishing can lead to a full breach
This is something I've learned over the years. Attackers change more quickly than we think they do. We make blind spots when we keep thinking that some platforms are safe.
Frequently Asked Questions
- What is the iOS exploit TA446 DarkSword?
It is a targeted cyberattack in which a group linked to a government uses an exploit kit to hack iPhones through phishing emails. - Is it possible to hack iPhones like this?
Yes. Advanced exploit kits can get around protections, but this is rare, especially on old systems. - Who is most likely to get hurt?
People in the government, researchers, journalists, and groups that work with sensitive information. - What can I do to keep my iPhone safe?
Keep your device up to date, don't click on links that look suspicious, and turn on security alerts. - Is this attack confirmed all over the world?
Some details have been confirmed by security companies, but the bigger picture may still be changing.
In conclusion
The TA446 DarkSword iOS exploit is not just another story about cybersecurity. It shows that attackers are changing the way they work.
Mobile devices are no longer secondary targets. They are very important to modern spying.
This is the most important thing to remember.
It's not enough to just protect laptops and servers anymore. The goal is to keep everything in your pocket safe.
And right now, that means more than ever.
It's time to look over your mobile defense plan if you're in charge of security at your company. Start by being aware, then learn how to spot threats, and finally become more resilient before attackers get there first.
Was this article helpful?
React to this post and see the live totals.
Share this :