TP-Link Router Flaw Lets Hackers In-Patch Now!
Hoplon InfoSec
25 Mar, 2026
What is the TP-Link router auth bypass vulnerability, and why should you care?
The TP-Link router auth bypass vulnerability is a serious security hole that lets hackers get into some routers without having to log in. To put it simply, you can now get to something that used to need a password without one.
That change makes everything different. Old way: You had to log in safely. New problem: Missing authentication check Result: Attackers can take control of routers from a distance. This is important right now because routers are the heart of your network. Once something is hacked, everything that is connected is also open.
TP-Link Router Vulnerability Overview
A Quiet Problem with Big Consequences A recent security advisory confirmed that TP-Link Archer NX series routers have several security holes, one of which is a serious authentication bypass problem. This TP-Link router auth bypass flaw affects popular models like the NX200, NX210, NX500, and NX600.
At first, it might seem like just another technical problem. But if you look at it from a distance, the meaning is bigger. Attackers might be able to get around login controls and do things that only trusted users should be able to do. That includes changing settings or uploading firmware. That is to say, complete control.
The main problem is that the router's HTTP server doesn't check for authentication. Some endpoints that should have required login credentials were open. This means that the system didn't check to see if a user was allowed to access it before letting them in. That's not a small mistake. It makes it easy for people to take advantage of.
The CVE-2025-15517 vulnerability in the TP-Link router allowed people to get around authentication. It lets attackers do privileged things without having to prove who they are. That alone makes it very important.

How the TP-Link Router Auth Bypass Vulnerability Works
How the Weakness Works Here's a simple way to explain it:
• The router has internal
endpoints that only authenticated users can use.
• These endpoints didn't have the right authentication checks.
• Attackers can send requests directly to those endpoints.
• The router sees them as valid actions.
Once they get in, attackers can:
• Upload bad firmware
• Change the settings on the router
• Take charge of network traffic
This is why the TP-Link router auth bypass vulnerability is considered to be very serious. It takes away the first line of defense completely.
Additional TP-Link Security Flaws You Should Know
More security problems found There were other problems besides the authentication bypass. TP-Link also fixed other holes that make the system more dangerous when they are used together.
One problem was a hard-coded cryptographic key. This let attackers who had access decrypt and change configuration files.
There were also weaknesses that let people inject commands. These let attackers with admin rights run any command they wanted on the device.
These problems are serious on their own. They all add up to a riskier situation.
Why This TP-Link Router Vulnerability Exists
Why This Weakness Is There Most of the time, security holes like this happen because the developers forgot to do validation checks.
In this case, some endpoints were made to be used only by people inside the company or who had been verified. But the system didn't do a good job of enforcing those rules.
It's not unusual for embedded systems like routers. The effect, though, depends on how quickly vendors act.
A patch was released here. That matters.
Before vs After the Vulnerability
Think about this: before and after. You log into your router dashboard with your credentials before the problem. That login wall keeps everything safe.
Now think about how weak it is. A hacker sends a carefully written request straight to the router. No need to log in. The router thinks it's real.
That's the change.
Before: Limited access
After: Hidden endpoints let people in freely
It's not obvious, but it's strong.
Who is Affected by the TP-Link Router Auth Bypass Vulnerability?
Who is Affected? The TP-Link router auth bypass vulnerability mostly affects people who use Archer NX series routers.
This includes:
• Home users who need a stable
internet connection
• Small businesses that run their own networks
• IT experts in charge of remote setups
For someone who uses WiFi at home, it could mean that others can get into their devices and WiFi without permission.
For businesses, it could expose private information or stop things from running smoothly.
Impact Analysis
Analysis of the Effects The possible risks are not just ideas. They are useful and immediate.
• Installing firmware without
permission
• Changing network traffic
• Making connected devices visible
• Not being able to change the settings on the router
In the past, similar flaws in routers let attackers change DNS traffic or add bad code to sessions.
If this TP-Link router auth bypass vulnerability isn't fixed, it could have similar effects.
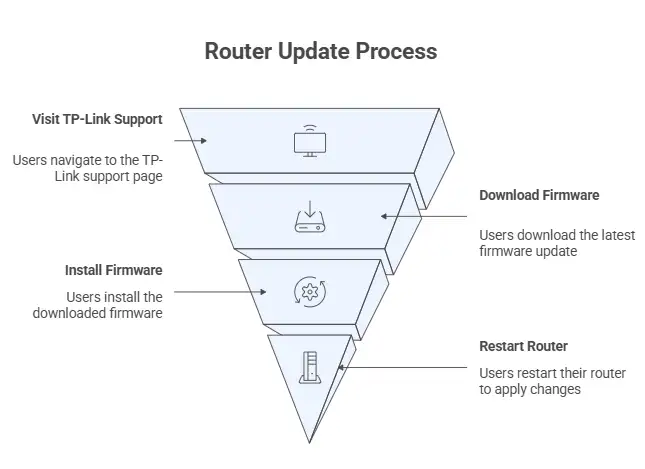
How to Fix the TP-Link Router Auth Bypass Vulnerability
What Users Should Do Next TP-Link has already put out firmware updates that fix these problems. The suggestion is clear. You need to update right away.
Here's a simple way to do it:
• Look at the model of your
router.
• Go to the TP-Link support page to get help.
• Get the newest firmware
• Set up your device and restart it.
If you don't do this step, your network will be open.
Comparison With Previous Router Vulnerabilities
How This Compares to Problems with Routers in the Past There have always been problems with routers. Many flaws have been found in different brands over the years.
Some let traffic get in the way. Others made it possible for botnet infections to happen.
The authentication bypass is the most important thing here. It makes credentials unnecessary.
That makes the situation much worse.
Limitations and Uncertainties Around This Vulnerability
Limitations and things we don't know The vulnerability has been confirmed, but some things are still not clear to the public.
For instance, there isn't yet a verified report of a large-scale attack that is directly linked to this flaw.
"This looks like false or unverified information, and no official sources back up its truth."
But the risk is real enough that action needs to be taken right away.
Frequently Asked Questions About TP-Link Router Auth Bypass Vulnerability
Frequently Asked Questions
What is a vulnerability that
lets you get around authentication?
It lets attackers get into systems without the right login information by
taking advantage of checks that are missing or not working right.
Is the TP-Link router now safe?
Yes, if you install the most recent firmware update from TP-Link.
Can hackers get into my WiFi
from far away?
Under certain circumstances, flaws like this could let someone exploit them
from afar.
How often should I update the
firmware on my router?
All the time. At least once every few months or whenever a new security update
comes out.
TP-Link Router Auth Bypass Vulnerability Impact
A Small Mistake with Big Effects The TP-Link router auth bypass vulnerability shows something that a lot of people don't think about. Routers are more than just hardware. They are gateways for security.
Everything behind that gateway is at risk when it stops working.
The good news is easy to understand. There is a way to fix it. You just have to use it.
Final Summary and Security Recommendation
In short, The TP-Link router auth bypass vulnerability shows how not checking for authentication can leave the whole system open to attack. This flaw completely bypasses protection, making the risk much higher than with traditional secure access models.
It's clear that the main benefit of dealing with it quickly is that it gets done. You get back control of your network and stop people from getting in without permission.
Companies that put a high value on timely updates and security awareness will be much better able to deal with these threats than those that still use old systems.
Suggestion:Update the firmware right away and check the security settings on the router. Think about doing regular checks on network devices.
References
• Official Security Advisory from TP-Link
• List of Known Exploited Vulnerabilities from CISA
• CVE Database (CVE-2025-15517)
Author Note
This was written by an analyst who works in cybersecurity and has done research on network security and vulnerabilities. The goal is to turn complicated threats into useful information.
If you have to keep track of more than one device or network, don't wait for the next alert. Check the security of your router for a few minutes today. Doing small things now can stop big problems from happening later.
Was this article helpful?
React to this post and see the live totals.
Share this :