Windows Defender 0-Day Vulnerability: BlueHammer, Risks, Fix
_compressed-20260417122628.webp&w=3840&q=75)
Hoplon InfoSec
17 Apr, 2026
Did a leaked Windows Defender 0-day vulnerability really turn into active attacks?
Yes. As of April 17, 2026, public reporting says the BlueHammer exploit and two related Windows flaws leaked by the same researcher are now being used in attacks, with BlueHammer reportedly exploited since April 10.
The most credible current public thread ties BlueHammer to CVE-2026-33825, a Microsoft Defender elevation-of-privilege issue patched in April 2026.
For readers landing here because they need a direct answer, here it is: the Windows Defender 0-day vulnerability story matters because it moved from a leaked proof of concept into reported real-world exploitation, and the end state is ugly.
A low-privileged local user can end up with SYSTEM-level control. For a home user, that can mean full device takeover after a single foothold.
For a business, it can turn a minor compromise into credential theft, lateral movement, and ransomware staging, potentially leading to significant financial loss and disruption of operations.
Technical Overview
|
Item |
Current public picture |
|
Public exploit name |
BlueHammer |
|
Publicly linked CVE |
CVE-2026-33825 |
|
Vulnerability type |
Local Privilege Escalation |
|
Impact |
Low-privileged user to SYSTEM |
|
Affected platforms in public reporting |
Windows 10, Windows 11, and supported Windows Server versions tied to Defender pre-April 2026 updates |
|
Severity |
CVSS 7.8 (High) in public technical reporting |
|
Patch status |
Microsoft shipped an April 2026 fix for CVE-2026-33825 |
|
Exploitation status |
Public reporting says BlueHammer has been exploited since April 10 |
|
Official sources to check |
Microsoft Security Update Guide, NVD, CISA KEV catalog, and Microsoft Defender Vulnerability Management |
The table above combines Microsoft, NVD, and independent technical reporting. One caution matters: Microsoft’s public-facing advisory text is brief, while third-party researchers published most of the exploit-chain detail. That means the CVE, impact class, and patch are well grounded, but some attack-flow specifics come from external analysis rather than Microsoft’s own write-up.
What is It?
BlueHammer
BlueHammer is the name given to a publicly released exploit that targets a Windows Defender 0-day vulnerability.
Security reporting and vendor analysis describe it as a local privilege escalation path. In plain operational terms, an attacker who already has a foothold as a standard user can climb to the highest local privilege level on the machine.
That is why the story traveled so fast. Defender is not some niche tool. It is the default security layer on a giant share of Windows systems. When an exploit abuses a trusted defender workflow instead of smashing memory the old-fashioned way, defenders lose one of their usual comfort blankets.
Why Zero-Day
It was called a zero-day because the exploit was public before an official fix was available. Microsoft’s own definition of a zero-day aligns with that framing, and BleepingComputer explicitly described BlueHammer as a zero-day when the exploit was released and no official patch existed yet.
Later, Microsoft addressed the issue in April's Patch Tuesday. At that point the story stopped being “an unpatched leak” and became “a publicly disclosed defender privilege-escalation flaw that now has a patch but also fresh evidence of exploitation.” This distinction is important for understanding search intent and for defenders who are triaging issues today.
Defender or Windows?
The honest answer is both, depending on what layer you are talking about. Public reporting consistently frames the situation as a Microsoft Defender elevation-of-privilege issue.
At the same time, the exploit chain reportedly abuses interactions between Defender behavior and trusted Windows features, which means that while Defender is the weak point, the practical risk extends to how these trusted features can be manipulated to compromise system security.
So the weak point appears in Defender, but the practical risk plays out across the Windows trust model.
Why This Matters
SYSTEM Access
On Windows, having SYSTEM access is a complete failure. That level of access lets an attacker bypass most user-level restrictions, tamper with security settings, create persistence, access protected data, and pivot into credential abuse.
Public technical reporting says BlueHammer can take an unprivileged account to NT AUTHORITY\SYSTEM.
That changes the conversation from “Can someone run something?” to “Can someone own the box after they get in once?” For incident responders, that is a much more expensive problem, as it can lead to full system compromise and unauthorized access to sensitive data and resources.
_compressed-20260417122628.webp)
Windows Defender 0-day vulnerability
Why LPE Matters
Many teams still under-rank local privilege escalation because it is not remote code execution. That is a mistake.
Real intrusions are usually chained. Phishing, browser compromise, malicious document execution, stolen low-privilege credentials, or remote access malware often provide the first foothold. Windows zero-day privilege escalation turns that weak foothold into real control.
For businesses, the outcome is the difference between one infected user and one compromised endpoint with authority to expose hashes, weaken protections, or move sideways. For home users, it is the difference between malware that is annoying and malware that survives cleanup attempts.
Our Technical Analysis
What stands out here is not only the bug. It is the trust boundary. Our read of the current public technical material is that BlueHammer is dangerous because it leans on legitimate Defender and Windows behaviors that defenders normally trust.
That makes detection harder, especially for teams that still over-rely on simple signatures instead of behavior-based telemetry.
That is also why this story has more staying power than a basic PoC drop. Once defenders realize a security product’s own workflow can be bent into a privilege path, they start asking a tougher question: what else in the same trust chain deserves review?
How It Works
Attack Flow
Public technical reporting describes how BlueHammer exploit works as a chain, not as a single magic packet. The write-ups point to a race condition and path handling issue in Defender’s remediation or update logic. The outcome is privileged file operations getting redirected in ways they should not, leading to unauthorized access to sensitive files and potential system compromise.
The important reader takeaway is simple. The attacker does not need kernel shellcode theatrics. The value comes from getting trusted Windows components to do dangerous work on the attacker’s behalf.
Update Abuse
Several security analyses say the exploit abuses Defender’s signature-update or remediation workflow. Field Effect’s summary says the flaw enables SYSTEM access by abusing the signature update process, while Core Security and Picus add technical context around remediation logic and file redirection or race-condition behavior.
This scenario poses a significant challenge for defenders. It is not just malware trying to disable Defender. Malware or an intruder may exploit trust associated with Defender to escalate their access.
Detection Gaps
Forbes cited Cyderes research, saying a Defender signature caught the original binary, but a basic recompile could evade that detection. Even if your mileage varies by environment, the lesson is solid: signature-only defenses are not enough when the attack technique lives in normal platform behavior.
Evasion Risk
That is why the Microsoft Defender zero-day exploit story is bigger than one GitHub repo. Once the technique is public, other actors can borrow the logic, swap binaries, and change timing. Defenders should expect variants.
Is It Exploited?
Leak Timeline
BlueHammer was publicly leaked in early April after the researcher behind it expressed frustration with Microsoft’s handling of disclosure. BleepingComputer reported the leak on April 6, while later coverage noted the patch did not arrive until the April 14 update cycle.
Public PoC
This was not rumor-only chatter. A working PoC was publicly released. That moved the issue out of abstract vulnerability discussion and into operator reality. Once usable code is loose, defenders have to assume copycats are coming.
Real Attack Risk
As of April 17, BleepingComputer reported that Huntress Labs had seen BlueHammer, RedSun, and UnDefend used in the wild and specifically said BlueHammer had been exploited since April 10.
That is the strongest current public support for calling this a Windows Defender actively exploited vulnerability.
CISA’s KEV catalog remains the official U.S. government source for known exploited vulnerabilities, but the search results available here do not confirm that CVE-2026-33825 is in KEV at this time.
So the cleanest wording is this: public reporting says the flaw is being exploited in attacks, while defenders should still check CISA KEV and Microsoft’s update guide for the latest official tracking status.
Who is Affected?
Windows 10 and Windows 11
Public technical reporting says the flaw can affect fully patched Windows 10 and Windows 11 systems before the April 2026 fix. Picus explicitly lists Windows 10 and Windows 11 supported versions in its affected-product summary.
Enterprises
Enterprises should care most. Why? Windows Defender's system access exploit paths are ideal for post-compromise upgrades. An attacker who lands as a user on a finance laptop, jump host, or developer workstation can turn that into meaningful privileges and data access fast.
Home Users
Home users are still at risk. A leaked Windows Defender vulnerability is still dangerous on a personal PC because malware does not need domain admin ambitions to ruin your week. SYSTEM access is enough to steal browser data, tamper with protection, and survive cleanup.
Patch Status
Before the Fix
Before April Patch Tuesday, BlueHammer was a true zero-day in the practical sense: public exploit, no official patch.
Microsoft Response
Microsoft’s Security Update Guide lists Defender vulnerabilities through the normal advisory process, and the April 2026 patch ecosystem clearly includes CVE-2026-33825 as a Microsoft Defender elevation-of-privilege issue.
Third-party patch analyses say Microsoft resolved it through updated Defender platform components, specifically addressing the vulnerabilities associated with CVE-2026-33825 to enhance security and prevent potential exploitation.
Latest Patch
Public reporting ties the fix to the April 14, 2026, Patch Tuesday cycle. Field Effect identifies the updated antimalware platform as version 4.18.26050.3011.
Remaining Risks
Patch status does not mean risk is zero. Systems can miss platform updates, stale golden images can linger, and detection content may not account for every exploit variation.
That is why asking,Is Windows Defender 0-day patched” is only half the question. The other half is, “Did the update actually land everywhere? That matters.”
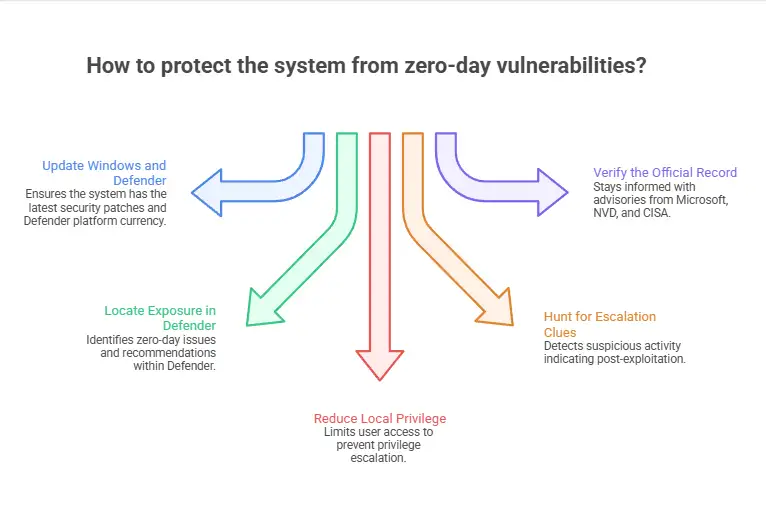
How to Protect Your System
Step 1: Update Windows and Defender
Apply the April 2026 Microsoft security updates and verify Defender platform currency. In managed environments, it is important to confirm that the endpoint is running the expected version of the Defender antimalware platform, rather than assuming that the status of Windows Update provides complete information.
Step 2: Locate Exposure in Defender
In Microsoft Defender, go to Exposure management and look for items tagged "Zero day" under vulnerability management. Microsoft documents this exact workflow for identifying zero-day issues, recommendations, and remediation tracking.
Step 3: Reduce Local Privilege
Review where standard users can execute untrusted code, create scheduled tasks, or write into sensitive paths.
BlueHammer is a local privilege escalation chain, so shrinking the initial foothold matters. This technique is one of the best answers to how to mitigate Windows Defender 0-day when patch rollout is still in progress.
Step 4: Hunt for Escalation Clues
Watch for:
Sudden jumps from standard user context to SYSTEM
Abnormal Defender-related process or service behavior
Unexpected task or service creation right after suspicious user execution
Credential access activity after local compromise
Those signals are consistent with the post-exploitation behavior researchers warn about, even if every attacker implementation looks slightly different.
Step 5: Verify the Official Record
Users should refer to official advisories from Microsoft, NVD, and CISA for the latest status. Microsoft is the authority on product updates, NVD provides the CVE framing, and CISA KEV is the best government tracker for confirmed widespread exploitation priorities.
Common Mistakes
The first mistake is assuming “local only” means “low risk.” That is not how modern intrusions work.
The second mistake is patching Windows but forgetting to verify Defender platform updates on every endpoint pool, VDI image, and server tier.
The third mistake is closing the ticket once the update lands. For a Windows Defender zero-day exploit explained properly, patching is the midpoint.
The final step involves verifying exposure, reviewing telemetry, and confirming that no exploitation occurred prior to the fix.
I cannot honestly claim we ran BlueHammer in a live lab for this draft, so I will not fake a war story. What we can say from reading the strongest technical analyses is that the exploit stands out because it appears to chain normal Windows features in ways that break defender assumptions. That is exactly the kind of issue that produces ugly surprises during incident response.
The practical lesson is familiar. The attacks that hurt the most are often not the loudest. They look like routine platform behavior right up to the moment they do not.
Security Checklist
Patch now
Confirm the April 2026 fix for CVE-2026-33825 is deployed and Defender platform versions are current.Validate exposure
In Microsoft Defender, review exposure management for zero-day-tagged recommendations and affected software.Hunt before closing
Look for recent privilege jumps, Defender-adjacent anomalies, and signs of credential access on endpoints that were unpatched during the leak window.
A leaked Windows Defender zero-day tied to BlueHammer is now reported as actively exploited, so unpatched Windows systems may be at immediate risk of SYSTEM-level compromise.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :