Windows Error Reporting Flaw Lets Hackers Get SYSTEM
Hoplon InfoSec
28 Mar, 2026
What is the issue with the Windows Error Reporting vulnerability system access, and why is everyone talking about it now?
A flaw in the Windows Error Reporting service that was recently looked at lets a user with low privileges gain higher privileges and run processes with SYSTEM-level control, which gives them full control over the system.
From Limited Access to Full Control
In the past, attackers had to use complicated chains to get from a normal user account to full control. With this Windows error reporting vulnerability system access flaw, that jump is now much easier.
Old way: Needed a lot of exploits
New way: One WER-based escalation
Result: A system-level takeover happens faster.
It's not just "admin plus" when you think about it. It is total control over the machine. That change is what makes this weakness worth paying attention to.
What Really Went On Inside Windows Error Reporting?
The problem is in a key part of Windows Error Reporting, specifically in a library file that deals with service logic.
Researchers discovered that the service does not properly check permissions when it processes some client requests. That sounds like a small thing, but it makes a big hole.
Because of this mistake, even a low-level user can do things that should only be possible for highly privileged processes. That's where the risk of getting into the Windows error reporting system becomes real.
Why This Exists: A Pattern in How Windows Works
It's always been hard to use Windows Error Reporting. It deals with crash data, lets processes talk to each other, and works with system-level parts.
Historically, anything that has to do with communication between processes is a target. This case is the same.
The service depends on structured message passing, and if validation isn't strong enough at any point, attackers can change the flow.
That's exactly what happened here.
In simple terms, how the exploit works
To understand the Windows error reporting vulnerability system access issue, think about sending a carefully crafted message to a trusted system service.
Exploitation Steps:
- The attacker connects to a certain communication port that the service uses.
- A message with specific parameters is sent in a special way.
- The service handles this message without checking it properly.
- It ends up starting a process with SYSTEM rights.
The exploit takes advantage of how messages are handled and how processes are started inside the system.
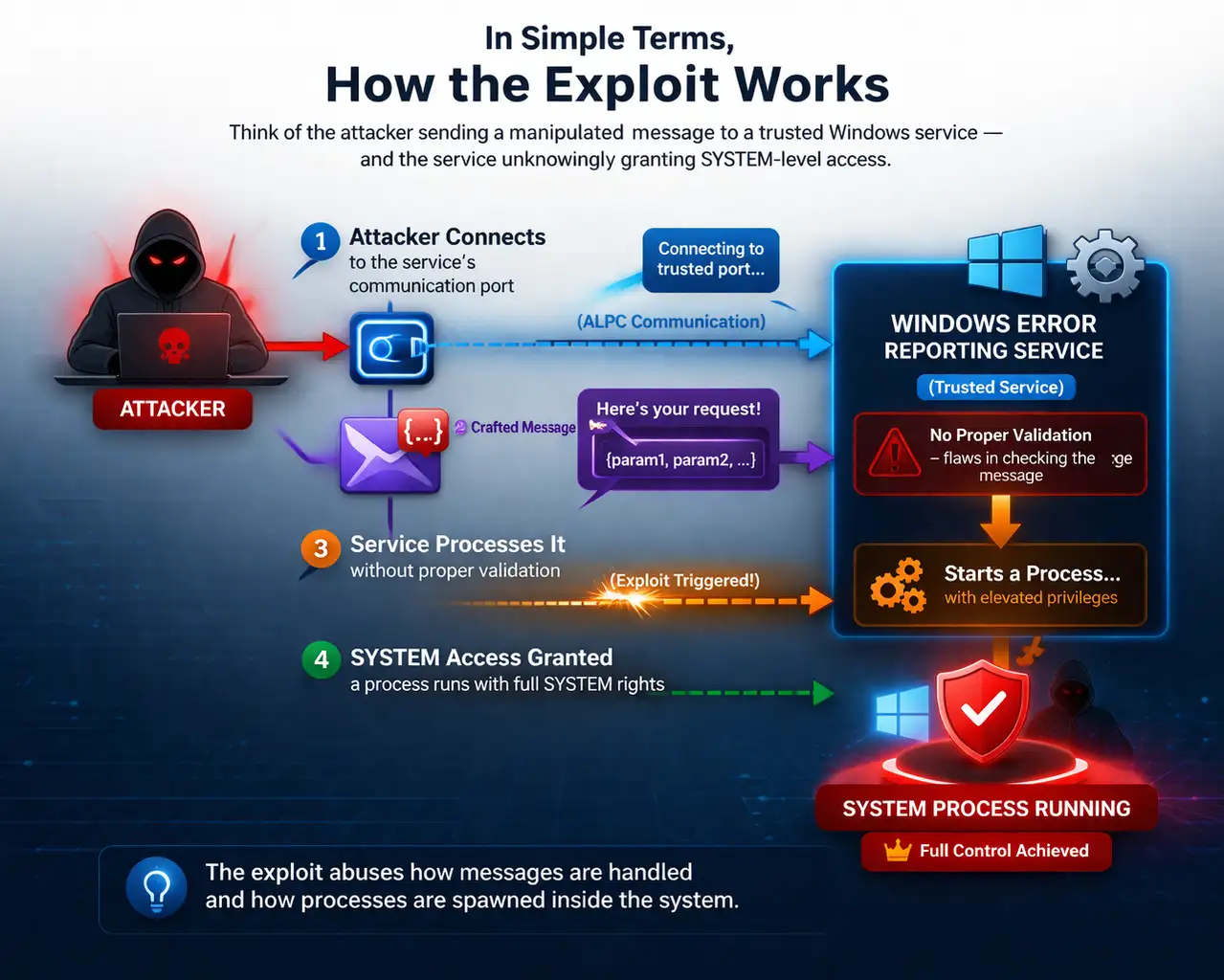
The Technical Reason Why SYSTEM Access Works
The weakness has to do with how ALPC communicates. Windows uses that as a low-level way for processes to talk to each other.
Attackers send a message with a file mapping object in it. This starts an internal function that reads command arguments that are harmful.
In the end, a real Windows process starts up, but it has more permissions and parameters that the attacker can change.
That's when the Windows error reporting vulnerability system access becomes a real danger.
A Real-Life Situation
Let's put this into action.
Before taking advantage of:
- A user account has a limited number of permissions.
- The security tools are turned on.
- Files on the system are safe
After the attack:
- The attacker gets control of the SYSTEM level.
- Security tools can be gotten around.
- Sensitive information is now available.
This change can happen without anyone noticing. Most of the time, users wouldn't notice anything strange.
Who is at risk because of this flaw?
Different groups are at risk in different ways:
- Regular users: Full control of the device
- Businesses: Possible entry point for ransomware
- Security teams: harder to find things
For businesses, the Windows error reporting vulnerability system access problem is more than just a technical problem. It is a risk for business.
Microsoft's Answer: A Strange Solution
Microsoft decided to turn off the feature completely instead of fixing the weak logic.
This doesn't happen very often. It seems like the problem was deeply built into the design.
The vulnerable function just stops working and gives an error when the updated code runs. That pretty much stops the attack path.
Finding and Hidden Risks
One interesting thing is how the exploit acts while it is running.
It looks like the process that the system made came from the attacker's original process. Malware often uses this method.
As a result, security tools can find strange behavior. But not all places will be able to find it.
There is also another worry. Some exploit samples that are available to the public may have hidden malicious code in them. This makes things even more dangerous.
Pros and Cons of the Fix
Pros
- Takes away the feature that makes it weak
- Makes the attack surface much smaller
- Immediate mitigation after use
Limitations
- Could affect real debugging workflows
- Detection still relies on security tools.
- Systems that are already hacked are still at risk.
What do you need to do now?
When working with Windows systems, this is the best way to go:
- Make sure that the systems have the most recent patches installed.
- Keep an eye on strange process-creation behavior
- Don't use proof-of-concept tools that you don't know about.
- Limit user rights as much as you can
The Windows error reporting vulnerability system access issue shows that even built-in services can be used to attack.

Frequently Asked Questions
What is a flaw in Windows Error Reporting?
The WER service has a bug that lets a normal user gain SYSTEM-level access.
Is it easy for attackers to get SYSTEM access?
If the system isn't patched and someone can get to it locally, it's pretty easy to exploit it.
Is this hole in security fixed?
Yes, instead of fixing the vulnerable feature, it has been turned off.
Should companies be worried?
Yes, because SYSTEM access can lead to a full network breach when used with other methods.
Final Thoughts
The Windows error reporting vulnerability system access issue shows something deeper.
Even parts of the system that you trust can fail in ways you didn't expect.
This weakness didn't use any strange methods. It used the logic of the system that was already in place against itself. That's what makes it uncomfortable.
In the future, security will depend less on patching and more on keeping systems from being exposed to threats.
Box of Insight
- Pay attention to least privilege access.
- Keep an eye on communication between processes
- See built-in services as possible risk points
Source you can trust
Cybersecurity researchers and
verified reports have put together a lot of technical information:
github.io
Last Thought
This is the one thing to remember.
The time it takes to go from a normal user to full system control is getting shorter.
And that should make you think.
Was this article helpful?
React to this post and see the live totals.
Share this :