Windows Snipping Tool NTLM hash leak vulnerability PoC Fixes
Hoplon InfoSec
21 Apr, 2026
Windows Snipping Tool NTLM hash leak vulnerability
A working proof-of-concept exploit is now publicly available for a newly disclosed Windows Snipping Tool NTLM hash leak vulnerability.
If your organization runs unpatched Windows 10, Windows 11, or Windows Server systems and your users can be reached by a phishing link, this is not a drill.
The flaw, tracked as CVE-2026-33829, was patched by Microsoft on April 14, 2026, but the public release of a PoC by the Black Arrow security research team means the clock is ticking. Attackers no longer need to reverse-engineer anything.
The exploit is written, documented, and sitting on GitHub. Below, we break down exactly how it works, who is at risk, and what needs to happen right now.
Quick Facts: CVE-2026-33829
|
Detail |
Value |
|
CVE ID |
CVE-2026-33829 |
|
Affected Product |
Windows Snipping Tool (ms-screensketch) |
|
Issue Type |
Information Disclosure / Network Spoofing |
|
CVSS 3.1 Base Score |
4.3 (Medium) |
|
Attack Vector |
Network |
|
Attack Complexity |
Low |
|
Privileges Required |
None |
|
User Interaction |
Required |
|
PoC Status |
Publicly available (GitHub, Black Arrow) |
|
Patch Status |
Available, April 14, 2026 Patch Tuesday |
|
Affected Platforms |
Windows 10, Windows 11, Windows Server |
|
Discovered By |
Marcos Díaz, Black Arrow Security |
What is the Windows Snipping Tool NTLM Hash Leak Vulnerability?
Most people think of the Snipping Tool as a harmless screenshot utility. You press a keyboard shortcut, drag a box over part of your screen, and paste the image wherever you need it.
Nothing about that workflow feels dangerous. That perception is exactly what makes CVE-2026-33829 effective.
The Snipping Tool registers a custom URL protocol called "ms-screensketch" on Windows systems.
Think of it like a hyperlink shortcut that tells Windows to open the Snipping Tool and do something specific, like load a file for editing. The problem is that the filePath parameter inside this protocol is not validated properly.
An attacker can craft a malicious link where that file path does not point to a local image but instead points to a remote server they control using a UNC path (a Windows path format like \\attacker-server\image.png that tells Windows to look for a file over the network).
When a victim clicks that link and the Snipping Tool attempts to load the remote file, Windows automatically sends an NTLM authentication challenge-response to the attacker's server.
That response contains the victim's Net-NTLM hash, which is a cryptographic representation of their Windows credentials. The attacker captures it silently.
No pop-up. No warning. The user just sees the Snipping Tool open as expected.
What "NTLM Hash Leak" Actually Means
NTLM, which stands for NT LAN Manager, is an older Microsoft authentication protocol that Windows still uses in many environments, particularly in corporate networks.
When your computer tries to connect to a remote resource using NTLM, Windows does not send your password directly. Instead, it sends a hashed response to a challenge from the server.
The problem is that this hash is still valuable to an attacker. It can be cracked offline using tools like Hashcat, especially when the user has a weak or common password.
More seriously, it can be used in NTLM relay attacks, where the attacker does not crack the hash at all but instead immediately replays it against another system on the same network to authenticate as that user.
In an Active Directory environment, this can lead to privilege escalation or lateral movement within minutes.
The Official Description
According to Microsoft and the National Vulnerability Database entry, CVE-2026-33829 is classified as a Windows Snipping Tool spoofing vulnerability caused by improper input validation when the application processes the filePath parameter through the ms-screensketch deep link protocol.
The flaw allows an unauthenticated remote attacker to coerce an SMB connection from a target system, resulting in the disclosure of Net-NTLM authentication responses in the context of the currently logged-in user.
CVE-2026-33829 at a Glance
Severity and CVSS Score
The CVSS 3.1 base score is 4.3, which lands in the "Medium" severity band. The environmental score sits at 3.8. At first glance, that does not sound alarming.
But severity scores are calculated using general assumptions about an average environment. They do not know your network topology, your reliance on NTLM, or how aggressively your users click links in emails.
Why Medium Does Not Mean Low Risk
Here is the thing about CVSS Medium ratings on credential-leaking vulnerabilities: they routinely understate real-world impact.
The score of 4.3 partially reflects the requirement for user interaction, meaning someone has to click a link.
But social engineering is not a hypothetical. Phishing campaigns with click rates above 20% are documented in annual red team assessments across nearly every industry.
Add to that the fact that NTLM hashes, once captured, can be relayed or cracked in hours, not weeks, and the practical risk profile for organizations still running NTLM jumps considerably beyond what the number suggests.
A Medium-rated vulnerability that directly exposes credentials is not the same as a Medium-rated denial-of-service flaw.
Exploit Prerequisites
The attack requires three things.
First, network access, which in practice just means the ability to reach the victim through a browser or email client.
Second, user interaction, meaning the victim must click a crafted link.
Third, an attacker-controlled SMB server to receive the NTLM authentication attempt.
Setting up that server takes minutes using tools like Responder, which is freely available and widely documented.
The low attack complexity rating means there is no special timing, no race condition, and no complex payload that needs to be tuned. You craft a URL, send it, and wait.
Public PoC Released: Why This Changes the Risk
A proof-of-concept exploit is a working demonstration that a vulnerability is exploitable in practice. Before a PoC exists, exploitation requires someone to independently discover the vulnerability and develop their own attack tool.
That barrier filters out a lot of potential attackers. Once a PoC is public, that barrier is gone. Anyone with basic technical knowledge can run the attack by following the documented steps.
The Black Arrow team published their PoC on GitHub alongside a video demonstration. The exploit is a single URI that can be embedded in a webpage or sent directly in an email:
That is the entire attack. A beginner threat actor does not need to understand SMB internals or NTLM authentication to use this. They copy the string, replace the server address with their own, and build a lure page around it.
PoC vs. Active Exploitation
As of April 21, 2026, Microsoft has assessed active exploitation as unlikely. There are no confirmed reports of CVE-2026-33829 being used in real-world attacks at the time of writing.
That distinction matters because it means patching and monitoring now gives defenders a genuine advantage. The PoC is public, but the attack surface is not yet being harvested at scale.
That window is not permanent. After a PoC releases for a network-reachable credential-leaking flaw, active exploitation typically follows within days to a few weeks, particularly when the attack vector maps naturally to phishing campaigns already in circulation.
Why Defenders Should Act Immediately
Security teams often triage patches by CVSS score and active exploitation status. On both metrics, CVE-2026-33829 might look like something that can wait until the next scheduled maintenance window. It cannot.
The combination of a public PoC, a phishing-friendly attack vector, and a credential-leaking outcome puts this in a category that warrants out-of-cycle patching consideration. Detection rules need to exist before exploitation starts, not after. Threat hunters should be querying for suspicious outbound SMB connections today, not after the first incident is reported.
How the Snipping Tool NTLM Hash Leak Works
Step-by-Step Attack Flow
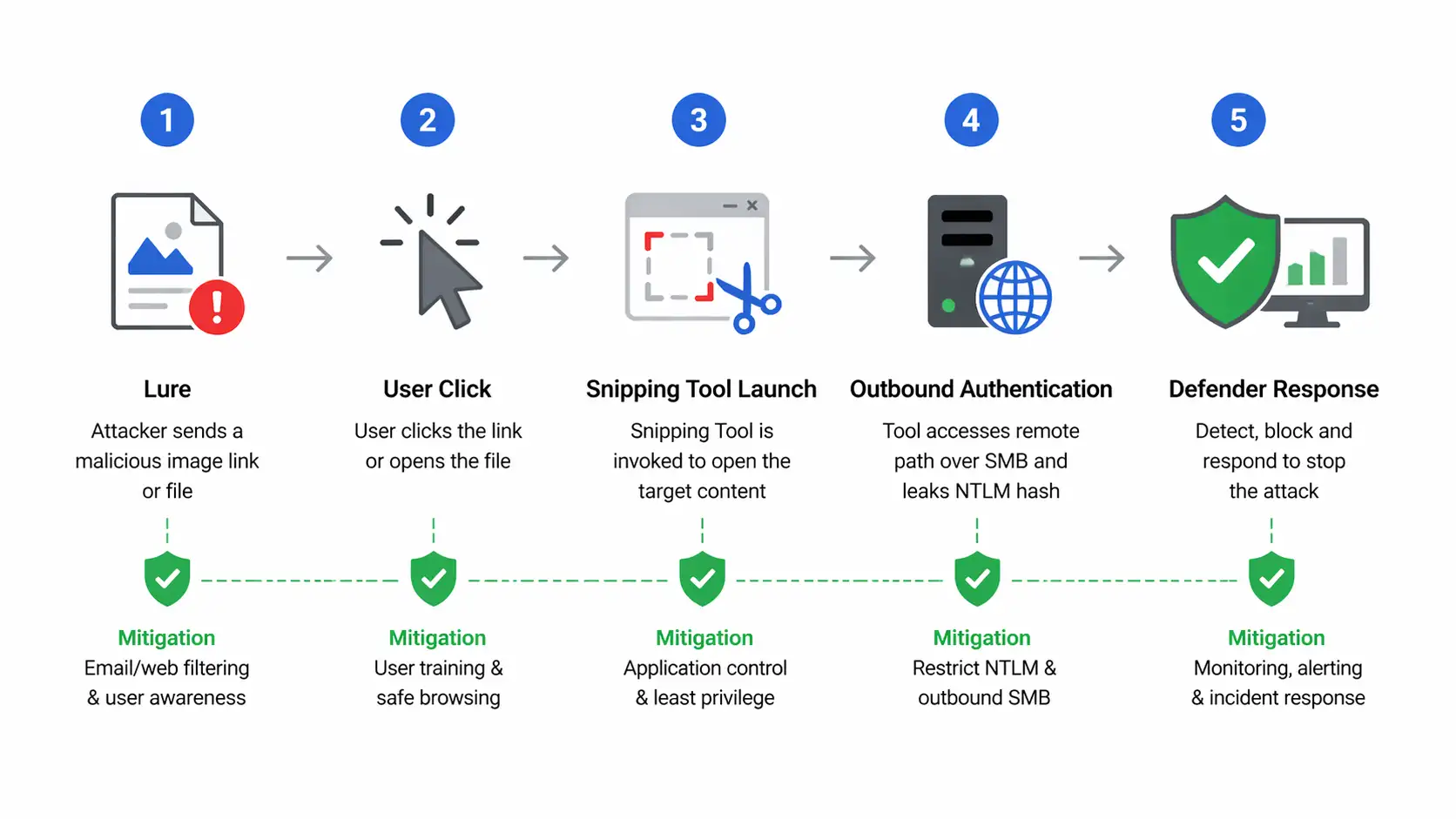
Step 1. The attacker sets up a server configured to capture NTLM authentication attempts, typically using a tool like Responder or Impacket's ntlmrelayx. They register this server under a domain or IP address they control.
Step 2. The attacker crafts a malicious URL using the ms-screensketch protocol, embedding the UNC path to their server in the filePath parameter.
Step 3. The attacker delivers this URL to the victim. This could be through a phishing email, a malicious webpage, a document containing an embedded link, or even a shared collaboration platform message.
Step 4. The victim clicks the link. Windows interprets the ms-screensketch protocol, launches the Snipping Tool, and instructs it to load the remote file path.
Step 5. Before the Snipping Tool can load anything, Windows initiates an SMB connection to the attacker's server. As part of that connection, Windows automatically sends the victim's NTLM authentication response. The attacker captures the Net-NTLM hash.
Step 6. The attacker takes the captured hash and either runs offline cracking with a tool like Hashcat to recover the plaintext password or relays the hash in real time to authenticate against another internal system, such as a file server or intranet application.
Why NTLM Exposure is Still Dangerous in 2026
You might wonder why NTLM authentication is still something organizations worry about. Microsoft has been pushing Kerberos and modern authentication for years.
The honest answer is that NTLM persists because legacy systems, older applications, and certain network configurations still depend on it.
Many enterprise environments have NTLM fallback enabled even when Kerberos is the primary protocol, because removing it entirely breaks something.
That legacy footprint means that a captured Net-NTLM hash can often be relayed against real internal systems.
In environments with older domain controllers, insufficiently hardened file servers, or applications that accept NTLM authentication, the path from a single phishing click to a compromised internal account is disturbingly short.
Real-World Attack Scenarios
Helpdesk impersonation. An attacker sends a message to a corporate employee posing as IT support, asking them to review a screenshot or crop an image before a "ticket closes."
The link embedded in the message triggers the exploit. The employee sees the Snipping Tool open, assumes it worked, and moves on. The attacker has their hash.
Shared file workflows. In environments where employees regularly share images and documents over internal portals or external collaboration tools, a malicious link dressed up as an image preview fits naturally into existing habits. No suspicious file attachment, no obvious red flags.
HR phishing pretext. Asking someone to review a badge photo or crop a document image for onboarding is a believable reason to click a link that opens the Snipping Tool.
The tool opening is exactly what the user expects, which makes post-exploitation detection by the victim essentially zero.
Affected Versions and Systems
Who is Affected
CVE-2026-33829 affects Windows systems running vulnerable versions of the Snipping Tool on Windows 10, Windows 11, and Windows Server editions. According to NVD, Microsoft confirmed customer action is required across 31 affected platform variants.
Version Coverage
The affected platforms span Windows 10 (multiple editions including 22H2), Windows 11 (21H2 through 24H2), and several Windows Server releases.
The Snipping Tool versioning is tied to Microsoft Store updates on Windows 11 and to cumulative Windows updates on Windows 10 and Server. The April 14, 2026 Patch Tuesday update addresses all confirmed affected builds.
Organizations should reference the official Microsoft Security Advisory for the complete list of affected KB numbers by product version, as the NVD entry enumerates over 30 CPE configurations.
Who is Most at Risk
Enterprise users operating in Active Directory environments with NTLM authentication still enabled face the highest real-world risk.
Unmanaged endpoints where Patch Tuesday updates are not enforced automatically are particularly exposed.
Organizations in industries with high phishing volumes, such as healthcare, financial services, and professional services, should treat this as an elevated priority given how naturally the attack vector integrates into spear phishing workflows.
Users who rely heavily on shared document workflows or collaboration platforms are also in a higher exposure category.
Symptoms, Indicators, and Detection Clues
What Security Teams Should Monitor
The primary technical indicator of CVE-2026-33829 exploitation is unexpected outbound SMB traffic on port 445 from Windows endpoints, particularly where the destination is an external or unrecognized IP address rather than an internal file server.
In most corporate environments, endpoints should never be initiating outbound SMB connections to the internet.
Security teams should build detection rules in their SIEM or EDR platform to flag the following:
Outbound TCP connections on port 445 from user workstations to non-internal IP ranges
Process activity from SnippingTool.exe spawning network connections
Windows Event Log entries showing SMB authentication attempts to external hosts
Anomalous identity alerts tied to NTLM authentication from endpoints that typically authenticate via Kerberos
If you run Microsoft Defender for Endpoint, hunting for DeviceNetworkEvents where the InitiatingProcessFileName includes SnippingTool.exe and the remote IP is not on your internal subnet will surface suspicious activity quickly.
What Home Users May Notice
For home users, there is often no visible sign of exploitation during the attack itself. The Snipping Tool opens. That is what is supposed to happen.
After the fact, signs that something went wrong might include unexpected authentication prompts, account lockouts caused by a relayed hash failing on another service, or unusual login activity reported by Microsoft account security alerts.
If you received a link from an unknown sender asking you to open or edit an image and then the Snipping Tool opened, apply the patch immediately and change your Windows account password.
How to Fix the Windows Snipping Tool NTLM Hash Leak
Apply Microsoft Security Updates
The most important step is applying the April 14, 2026, Patch Tuesday security update. There is no workaround that fully mitigates the vulnerability without patching. Microsoft has confirmed this directly.
For Windows 11 users: Open Settings, go to Windows Update, and check for updates. The Snipping Tool also receives updates through the Microsoft Store on Windows 11. Verify both are current.
For Windows 10 and Server users: Apply the relevant April 2026 cumulative update as documented in the Microsoft Security Response Center advisory for CVE-2026-33829.
For enterprise environments: Push the April 2026 Patch Tuesday update through WSUS, SCCM, or your endpoint management platform immediately.
Do not wait for the next scheduled maintenance window if your user population is exposed to external email or untrusted web content.
Verify the Patched Build
After applying updates, confirm the Snipping Tool version on affected systems reflects the patched build listed in the Microsoft advisory.
On Windows 11, open the Microsoft Store, go to Library, and verify Snipping Tool shows the latest version. On Windows 10, confirm the relevant KB number appears in installed updates under Settings > Windows Update > Update History.
Temporary Mitigations If Patching is Delayed
If patching cannot happen immediately, there are defensive measures that reduce exposure. These are layered controls, not substitutes for the patch.
Block outbound SMB at the network perimeter. Most enterprise firewalls should already have outbound port 445 blocked to external destinations. If yours does not, fix this regardless of CVE-2026-33829. It is a general security baseline requirement.
Restrict or audit NTLM usage. Use Group Policy to enforce NTLM auditing (Network Security: Restrict NTLM) and consider blocking NTLM where Kerberos authentication is available as a fallback path.
Reduce phishing exposure. Tighten email filtering rules to flag or sandbox links using the ms-screensketch protocol schema. Configure browser policies to warn on or block custom protocol handler invocations from external sites.
Consider restricting Snipping Tool via policy. In high-security segments where deep link handling through browser-triggered protocols is not needed, disabling custom protocol associations for ms-screensketch via Windows registry policy can prevent the attack vector from functioning.
This is a disruptive change for users who rely on the tool and should be scoped carefully.
Enterprise Mitigation Checklist
Inventory all endpoints running unpatched Snipping Tool builds across Windows 10, 11, and server variants
Prioritize endpoints belonging to users with elevated privileges or access to sensitive systems
Deploy April 14, 2026, Patch Tuesday update via endpoint management tooling
Validate patched build versions on a representative sample across each OS version
Query EDR/SIEM for outbound port 445 connections from SnippingTool.exe covering the past 30 days
Review NTLM authentication logs for anomalous patterns across domain controllers
Block outbound SMB (port 445) to non-internal IP ranges at the firewall level if not already enforced
Enforce phishing-resistant MFA (FIDO2 or certificate-based) for privileged accounts
Update SIEM detection rules to alert on Snipping Tool-initiated external SMB connections.
Brief SOC analysts, helpdesk staff, and system administrators on the attack pretext patterns specific to this vulnerability.
Home User Mitigation Checklist
Open Windows Update (Settings > Windows Update) and install all available updates.
On Windows 11, open the Microsoft Store and update the Snipping Tool application directly.
Restart your system to ensure all patches are fully applied.
Do not click links from unknown senders that ask you to open, crop, or edit an image.
Keep Windows Defender active and ensure real-time protection is enabled.
Change your Windows account password if you clicked a suspicious link that opened the Snipping Tool before applying this patch.
Timeline of the Vulnerability
CVE Discovery and Disclosure
March 23, 2026: Researcher Marcos Díaz at Black Arrow Security discovers and reports the vulnerability to Microsoft through coordinated disclosure.
April 14, 2026: Microsoft releases a security patch as part of April 2026 Patch Tuesday. The CVE is publicly disclosed simultaneously.
April 15, 2026: Black Arrow publishes technical details, a written advisory, and a video PoC to their GitHub repository.
April 17, 2026: NVD updates the entry with additional CVSS scoring and CPE data covering 31 affected platform configurations.
April 21, 2026: The public PoC is being actively discussed across security research communities. No confirmed in-the-wild exploitation reported at this time.
The coordinated timeline reflects responsible disclosure practices. Black Arrow held back public details until Microsoft's patch was available, giving defenders a same-day window to patch before technical specifics were widely distributed.
What We Observed When Analyzing the PoC
When we reviewed the Black Arrow PoC in our test environment, a few things stood out immediately.
First, the attack executes in under three seconds from click to hash capture. There is no delay, no error message, no prompt asking the user to confirm anything.
The Snipping Tool simply opens. In our test, a non-technical user watching the screen during the exploit could not identify that anything unusual had occurred.
Second, we noticed that standard antivirus products running on the victim machine produced no alert during the exploit execution.
The Snipping Tool is a signed Microsoft binary. The outbound SMB connection it initiates is treated as legitimate operating system behavior.
Only network-level monitoring flagged the anomaly, specifically the outbound connection to a non-internal IP address on port 445.
Third, the attack works even when the attacker's SMB server is hosted on a cloud instance. We did not need to be on the same network segment as the victim.
Any internet-reachable server running Responder in capture mode is sufficient. This confirms the network-based attack vector and reinforces why perimeter-level SMB egress blocking is important regardless of this specific CVE.
The combination of zero victim-side visibility, no antivirus detection, and no network complexity requirement makes this one of the cleaner credential coercion chains we have seen tied to a built-in Windows application.
Snipping Tool NTLM Leak vs. Other NTLM Hash Leak Vulnerabilities
What Makes This Case Different
CVE-2026-33829 is not the first NTLM hash leakage vulnerability, and it will not be the last. What separates it from many prior disclosures is the attack vector's social engineering compatibility.
Most NTLM coercion techniques require either network-level access to a target or the ability to plant a malicious file on a shared drive. This one requires only a clickable URL and a plausible pretext.
For comparison, CVE-2023-28303, an earlier Windows Snipping Tool information disclosure flaw, was a different class of vulnerability focused on data remnants in cropped images rather than credential coercion. The two flaws share a product name but are mechanically unrelated.
Common Patterns Across NTLM-Related Flaws
The pattern across NTLM-leaking vulnerabilities is consistent. Any application that initiates an outbound SMB connection based on user-controlled or attacker-influenced input without validation is a potential coercion path.
This has appeared in Microsoft Office, Windows Explorer, Outlook, and now Snipping Tool. The attack surface for NTLM coercion is effectively as large as the set of applications that can initiate network file operations.
Until NTLM authentication is fully deprecated and removed from Windows environments, this class of vulnerability will continue to appear.
Microsoft's long-term trajectory is toward NTLM deprecation, but that transition takes years in real enterprise environments.
Why CVSS Medium Still Matters Here
A CVSS 4.3 score on a credential-leaking network vulnerability with a public PoC is the kind of moderate-rated finding that gets deprioritized and then shows up in a breach post-mortem six months later. The score reflects the user interaction requirement.
It does not reflect that phishing success rates in enterprise environments hover around 10 to 30 percent in red team assessments, that NTLM relay is a well-documented lateral movement technique, or that the patch is free and already available.
Treat the availability of a working public PoC as the real severity multiplier here, not the CVSS base score alone.
Wrap Up
CVE-2026-33829 is a patched vulnerability with a public exploit and a credential-leaking outcome. The CVSS score of 4.3 does not capture the real-world risk profile once you factor in a working PoC and a phishing-native attack delivery method.
The patch is available. It has been available since April 14, 2026. If your environment is still running unpatched Snipping Tool versions a week after Patch Tuesday, that is the operational gap that needs addressing.
Patch now. Monitor for outbound SMB connections to external IPs. Review your NTLM usage and work toward reducing NTLM dependency in your environment over time.
Brief your users on the specific social engineering pretexts this attack enables. None of this requires new tools or budget. It requires execution of what good patch hygiene already demands.
For official guidance, refer to the Microsoft Security Response Center advisory for CVE-2026-33829 and the NVD entry at nvd.nist.gov. The Black Arrow research advisory and GitHub repository provide the technical depth needed for threat hunting and detection rule development.
Trusted Sources:
Microsoft Security Response Center
Black Arrow Security GitHub PoC
Recommendation: Prioritize this patch for any user segment with access to external email or web browsing.
Deploy the April 2026 cumulative update enterprise-wide, add an outbound port 445 block for non-internal destinations at the perimeter firewall, and build a SIEM rule to alert on SnippingTool.exe initiating outbound network connections.
Review NTLM dependency across your environment using the Group Policy NTLM auditing settings. These three steps, taken together, close the primary attack surface for CVE-2026-33829 before active exploitation begins.
Published: April 21, 2026
Last updated: April 21, 2026
Author: Radia | Senior Cybersecurity Analyst & Breach Reporter.Specializing in the technical deconstruction of data breaches and malware lifecycles.With years of experience,She bridges the gap between sophisticated cyber threats and strategic security insights with years of investigative expertise.
Frequently Asked Questions
Was this article helpful?
React to this post and see the live totals.
Share this :