Latest Cybersecurity Threats: Weekly Recap of Silent Digital Attacks

Hoplon InfoSec
06 Feb, 2026
A recap of what happened this week
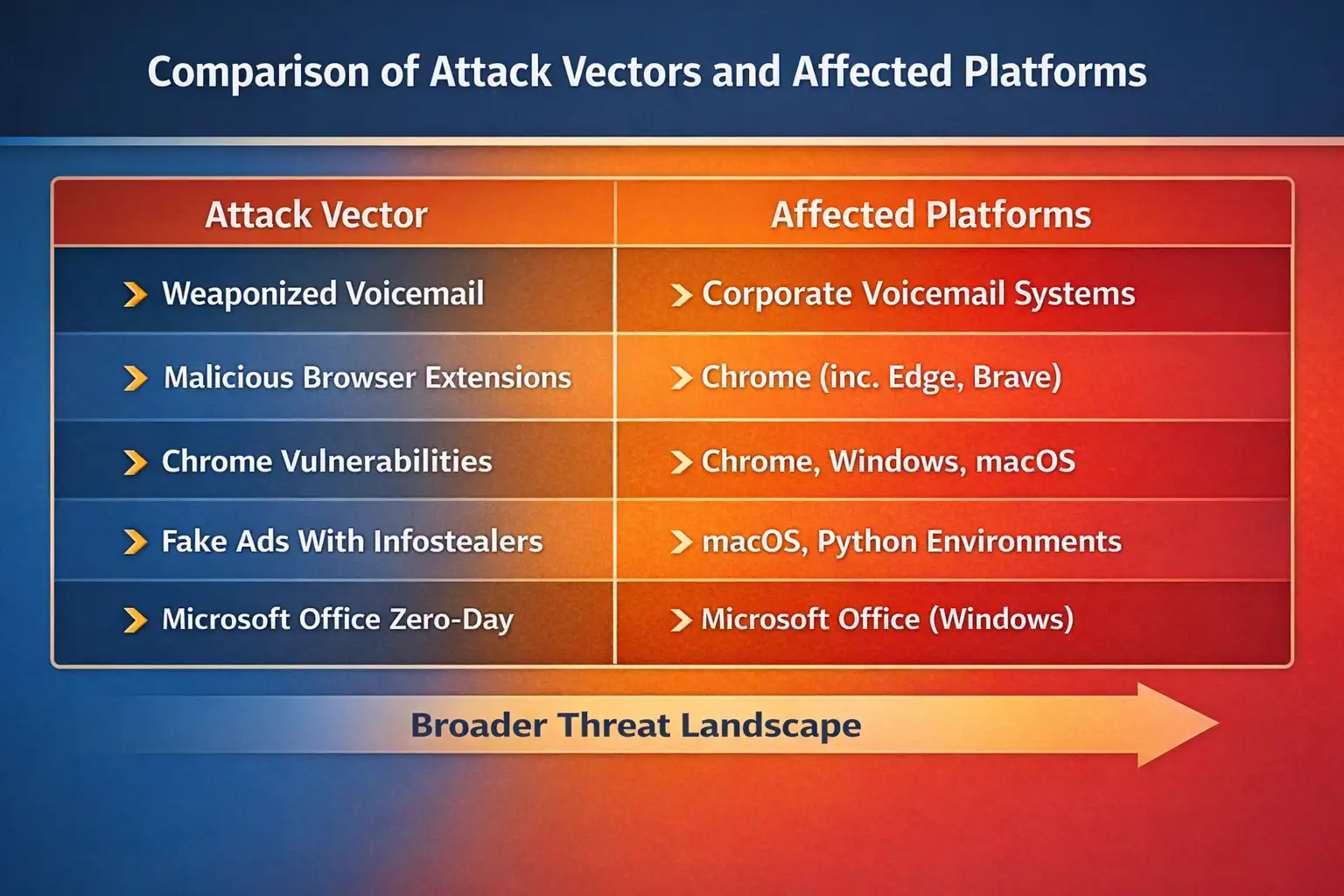
This weekly cybersecurity recap puts together a number of incidents and research findings that, on their own, might not seem connected. Attacks that use voicemail as a weapon. Redirecting traffic on NGINX servers. Chrome vulnerabilities used without anyone knowing. Fake ads are targeting macOS users. APT28 is using Microsoft Office for its own ends. Bad browser extensions that misuse ChatGPT access.
It's hard to miss a pattern when you look at them all together.
Attackers are no longer breaking in with loud noises. Instead, they are becoming part of everyday work. Systems for phones. Browsers. Ads. Add-ons. Even tools that are supposed to keep you safe.
The effect is not limited to one country or platform. This week, reports mentioned Windows, macOS, Linux, mobile devices, and cloud servers. This is important right now because so many people are seeing it.
Why You Should Read This Cybersecurity Weekly Recap
A lot of people read security news quickly to find one big breach. That way of thinking is old-fashioned. This weekly recap of cybersecurity shows something less obvious but more dangerous.
Most of the things that happened this week didn't depend on new zero-day exploits. Instead, attackers used features that were already there in ways that weren't expected. Voicemail systems turned into entry points. Chrome add-ons turned into data thieves. At the server level, traffic redirection happened without anyone knowing.
The real danger is being too comfortable. These attacks work because they seem normal. No pop-ups. No notes about ransomware. No clear signs of trouble.
Weaponized voicemail attacks are no longer just a theory
What Went Wrong
Researchers in security found that voicemail systems were being abused in the real world, with attackers using fake audio files and signaling tricks to get remote access. In some cases, all the user had to do was listen to a voicemail.
This is not a hack like in Hollywood. Many companies forgot they even had legacy telecom integrations, which is a practical abuse.
Why It Matters
Voicemail systems are often not monitored for security like other systems are. People see them as utilities, not endpoints. Once they are hacked, they can be used for social engineering or to get into internal networks.
Voicemail stands out in this weekly cybersecurity recap because it targets trust. People believe phone systems more than email links. That assumption is now dangerous.
Read more
Simple Explanation of NGINX Traffic Redirection Attacks
What Went Wrong
Researchers saw NGINX servers being changed so that visitors would be sent to places controlled by attackers. The servers themselves stayed online and looked normal to the people in charge.
The attack was more about changing settings than putting malware on computers.
Effect on the Real World
Traffic redirection can quietly steal your login information, add ads, or send you to phishing pages. Companies might not notice until customers complain.
This weekly cybersecurity recap shows that server misconfigurations are still one of the best ways for attackers to get in, even in cloud environments.
Risks of Chrome vulnerabilities and running arbitrary code
What took place
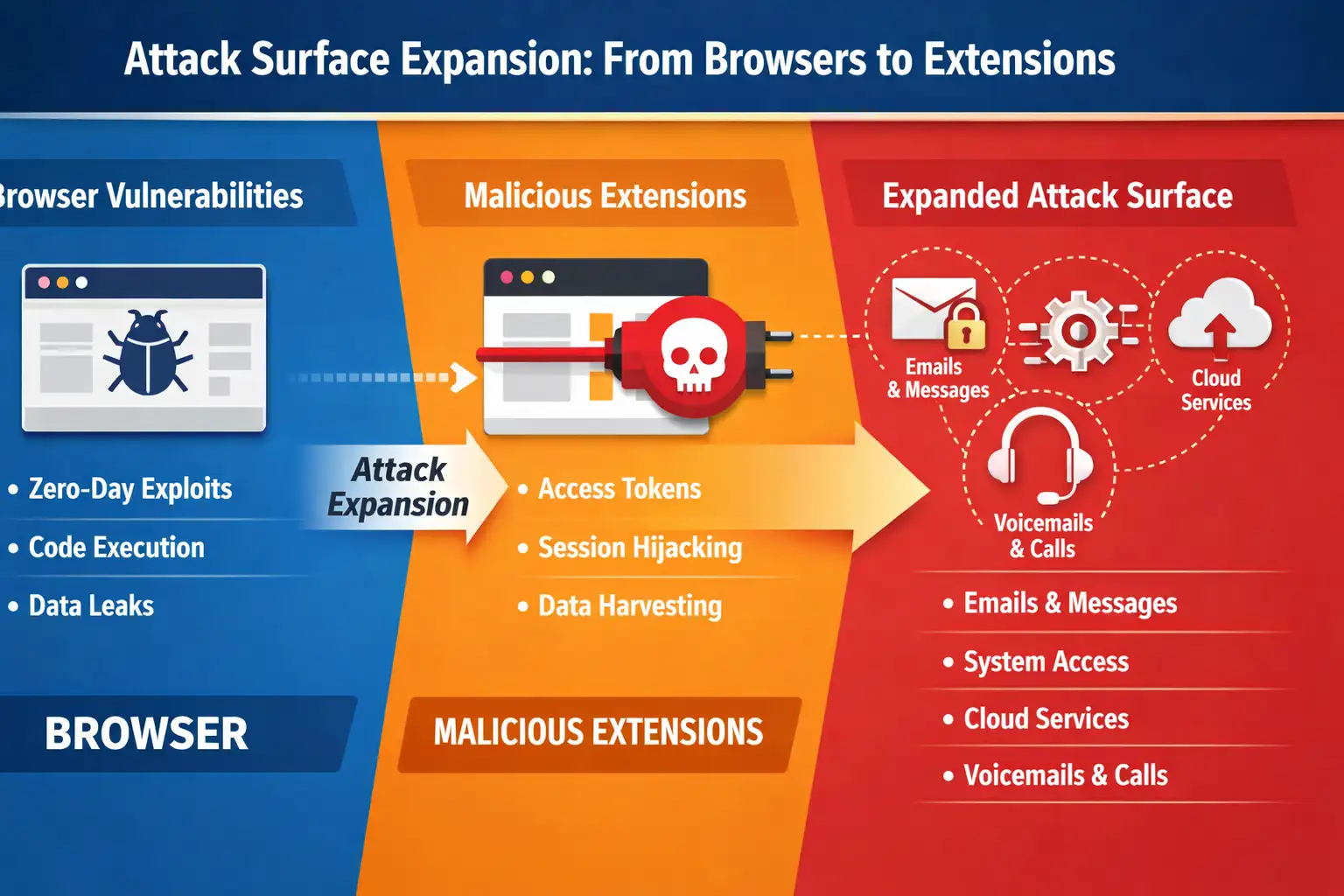
There were several Chrome security holes that could let attackers run any code they wanted if they were able to take advantage of them. Some people were already taking advantage of the flaws before the patches were widely used.
There is no public confirmation that every vulnerability was used on a large scale. It's important to be clear about that uncertainty.
Why Users Should Care
Chrome isn't just a web browser. It is a platform for applications. Attackers can often get to saved credentials, sessions, and extensions when they can run code inside it.
In this weekly recap of cybersecurity news, Chrome comes up again later for a different reason: bad extensions.
Malicious Chrome Extensions Taking Advantage of ChatGPT Access
What Went Wrong
Several Chrome extensions were found to be stealing ChatGPT sessions and tokens. On the surface, the extensions looked useful and real.
They didn't take advantage of ChatGPT itself. They took advantage of user trust and browser permissions.
Why This Matters
AI tools are becoming more common in everyday tasks. When extensions misuse access, private conversations and business information can leak without anyone knowing.
This weekly cybersecurity summary shows that AI security is more than just models. It's about the environment they live in.
Fake ads and Python infostealers are targeting macOS users
What Went Wrong
Microsoft said that infostealers that use Python are going after macOS users with fake ads. People who were hurt were tricked into downloading software that looked real.
After it was installed, the malware focused on stealing passwords and data from browsers.
Context and Limits
It wasn't clear that all of the campaigns were big. There are still investigations going on into some reports. That uncertainty doesn't lower the risk.
This weekly cybersecurity summary makes it clear that macOS is no longer a low-priority target.
APT28 and Microsoft Office Zero-Day Activity
What Went Wrong
APT28, a well-known group of hackers, was connected to the use of a zero-day vulnerability in Microsoft Office. The exploit let bad code run through specially made documents.
Microsoft sent out warnings and advice on how to fix the problem.
Why It Matters for Strategy
APT28 often goes after governments, the media, and policy groups. But collateral exposure also hurts other people.
This cybersecurity weekly recap uses this event to show that even advanced hackers still use tools they know, like Office documents.
New system file access controls come with Windows 11
What Changed
Microsoft has announced a new Windows 11 security feature that will limit access to system files. The goal is to cut down on the abuse of malware and other tools that aren't authorized.
Real-World Effects
Security features only work if you know how to use them. Companies will need to carefully check for compatibility.
This weekly cybersecurity recap includes this update because changes to defenses are just as important as attacks.
Find and remove the Tamecat PowerShell backdoor
What Went Wrong
Researchers wrote down how to find and get rid of the Tamecat PowerShell backdoor. The malware used built-in scripting tools to hide in plain sight.
Why It's Hard
PowerShell is a real and powerful tool. It is not possible to completely block it.
This weekly recap of cybersecurity talks about how hard it is to tell the difference between normal administration and bad behavior.
A Look at Pentesting Tools and AutopentestX
What Was Looked At
We looked at AutopentestX, a Linux-based penetration testing tool, to see what it could and couldn't do. It is mostly about automation and reporting.
A Fair View
Defenders can use tools like this, but they can also be misused. It is very important to have context and permission.
This review is part of this week's cybersecurity recap to stress the importance of responsible security testing.
Mobile device security audits are becoming more important
What Changed
More and more businesses are looking for services that audit the security of mobile devices. This demand is growing because more people are working from home and using their own devices.
Why It's Important
Phones now have business email, authentication apps, and private information on them. But they are often watched less than laptops.
This weekly cybersecurity recap shows that mobile security is no longer a choice.
This Week's Cross-Cutting Themes
A few patterns stand out.
First, attackers like places that are easy to get into. Voicemail. Ads. Add-ons. Files for setting up.
Second, trust is the thing that gets used the most. People trust browsers. Servers are trusted by admins. People trust documents.
Third, the biggest problem is still visibility gaps.
This weekly roundup of cybersecurity news isn't meant to scare you. It has to do with being realistic.
What Users and Businesses Should Do Next
There is no one solution that works for everything. But taking action helps.
Check your browser extensions often. Be very strict about permissions.
Check the settings on your servers, not just the software versions.
Consider voicemail and phone systems to be security assets.
Turn on new OS protections when you can.
Don't just look at signatures; also look at behavior.
This weekly recap of cybersecurity is a reminder that the basics are still important.
Questions that are asked a lot
What is the most important thing to remember from this weekly cybersecurity recap?
The most important thing to remember is that modern attacks don't announce themselves; they blend in with normal activity.
Are these attacks confirmed on a large scale?
Some are confirmed, but others are still being looked into. When there isn't confirmation, it's clear that there is uncertainty.
Should people who aren't tech-savvy be worried?
It's okay to be worried, but not to panic. Awareness and basic hygiene reduce most risks.
Is macOS now as easy to hack as Windows?
Different threats exist for each platform. Neither should be thought of as safe by nature.
How often should businesses check their browser add-ons?
At least once every three months, and right after any event that exposes data.
The Hoplon Insight Box
Main Suggestion:
Companies should make a list of systems that are often forgotten, like voicemail, browser extensions, and mobile devices. Because they are not part of normal security monitoring, these areas keep coming up in incidents.
Final Thoughts
This weekly roundup of cybersecurity news isn't about getting headlines. It's about being aware of how the threat landscape is changing without making a big deal out of it.
The attacks we talked about this week didn't depend on chaos. They depended on comfort. Tools, you know. Normal behavior. Thought to be safe.
In 2026, being safe is more about paying attention early than reacting quickly.
Was this article helpful?
React to this post and see the live totals.
Share this :