Weekly Cybersecurity Recap: Fake Apps & iPhone Risks
-20260403134259.webp&w=3840&q=75)
Hoplon InfoSec
03 Apr, 2026
What happened this week in cybersecurity?
What happened this week, April 3, 2026? In one sentence: users and IT teams were hit with a messy mix of fake mobile apps, fresh iPhone exploit concerns, emergency Windows fixes, developer phishing traps, and a confirmed cloud breach at a major public institution. Apple published security releases for iOS 26.4 and also pushed iOS 18.7.7 for older users, Microsoft documented both KB5079391 and the follow-up KB5086672, and the European Commission confirmed that data was taken from systems supporting the Europa web platform.
That is why this weekly cybersecurity recap matters. These stories are not abstract policy notes for security teams in a back room. They affect iPhone owners who postpone updates, Windows users who ignore out-of-band fixes, developers who trust GitHub notifications a little too quickly, and organizations that assume cloud hosting automatically means resilience. In plain English, the week’s lesson is simple: familiar brands still attract unfamiliar risks.
Why this week’s stories matter more than usual
A lot of security weeks feel noisy. One breach here, one patch there, another threat report that never reaches ordinary users. This one felt different because the stories touched multiple layers of the digital stack at once. Messaging apps, operating systems, developer tools, public-sector cloud infrastructure, and even a high-profile personal email compromise all landed in the same news cycle. That concentration changes user behavior. It creates confusion, patch fatigue, and an opening for attackers who thrive when people stop reading carefully.
There is also a pattern here that deserves attention. The biggest theme is not just malware or spyware. It is trust hijacking. Attackers are dressing malicious activity in the look and feel of legitimate services, whether that means a fake WhatsApp client, fake VS Code alerts delivered through GitHub workflows, or phishing and breach narratives wrapped around real brand names. That makes this weekly cybersecurity recap useful as more than a list of incidents. It is a map of how attackers are trying to blend into normal digital life.
Fake WhatsApp spyware app warning raises mobile trust concerns
One of the most unsettling stories involved warnings about a fake WhatsApp app used to spy on users, with reports centering on targets in Italy. Public reporting says affected users were tricked into installing an unofficial version of WhatsApp outside Apple’s official App Store, and WhatsApp indicated that the issue was tied to a counterfeit client rather than a breach of WhatsApp’s core platform. That distinction matters. The app most people trust was not “hacked” in the way headlines sometimes imply. The danger came from sideloading or unofficial distribution.
For regular users, this is the part worth remembering. A fake app does not need to look wildly suspicious anymore. It only needs to look close enough during a moment of urgency. Someone receives a link, gets a rushed message about an account issue, or is told to install a “secure version,” and suddenly the guardrails are gone. Mobile attacks increasingly borrow the language of support, compliance, and safety. That is exactly why stories like this belong in any serious weekly cybersecurity recap. They show how social engineering keeps evolving even when the platform itself is not directly broken.
It is also fair to add a note of caution. Some online descriptions of this campaign are still thin on technical detail. Where reporting could not be verified through official disclosures, the safest conclusion is this: the risk appears real, but not every circulating claim has been independently confirmed. This appears to be unverified or misleading information in some retellings, and no official source confirms every dramatic version of the story. That nuance matters if you want trustworthy coverage instead of recycled panic.
-20260403134259.webp)
DarkSword pushes Apple into a more urgent patch posture
The Apple side of this weekly cybersecurity recap was bigger than a routine patch note. Apple’s security releases page shows iOS and iPadOS 26.4 as current, and Apple also published security content for iOS 18.7.7 and iPadOS 18.7.7, noting that availability was expanded on April 1, 2026 so users with Automatic Updates could receive protections against web attacks tied to DarkSword. That is notable because it means Apple was not only pushing the newest release forward. It was also moving to protect users who had stayed behind on an older major version.
Security researchers have described DarkSword as a serious iOS exploit chain. Google Threat Intelligence Group said it observed a full-chain exploit leveraging multiple zero-days, and public reporting later highlighted how unusual Apple’s backported response was for users still on iOS 18. In security terms, that is a sign that the risk was too meaningful to leave behind a large population of users who had not upgraded.
That makes the Apple story unusually practical. If you own an iPhone and you tend to delay upgrades because you dislike interface changes, this week was a reminder that the threat landscape does not care about your aesthetic preferences. Attack chains become more dangerous once they are documented, discussed widely, or leaked in ways that lower the skill barrier for attackers. So yes, the safest move is still to update. And yes, this is exactly the sort of consumer-facing alert that deserves a high place in a weekly cybersecurity recap.
Windows 11 KB5079391 and KB5086672 show why “optional” does not always feel optional
Microsoft’s Windows update story was less flashy, but honestly more relatable for office users. The company’s March 26, 2026 entry for KB5079391 described the release as a non-security preview update for Windows 11 25H2 and 24H2. Then, just days later, Microsoft published KB5086672 as an out-of-band update that included the earlier improvements and added a fix for an installation problem affecting some devices. That sequence tells you a lot about modern Windows servicing. Even “preview” updates can become part of a practical troubleshooting chain.
This is where many users get tripped up. They see “preview” or “optional” and assume it is safe to ignore everything in that lane forever. Sometimes that is reasonable. Sometimes it is not. When Microsoft issues a follow-up out-of-band release to resolve install issues, the conversation shifts from feature curiosity to operational stability. In a business environment, that changes patch planning, help desk advice, and user trust in Windows Update itself.
The broader lesson for this weekly cybersecurity recap is not that every Windows update is a crisis. It is that update hygiene has become more layered. Security fixes, quality improvements, known issues, and emergency repairs now arrive in a cadence that ordinary users rarely track closely. The safest habit is to read the release notes for your version and avoid guessing based on social posts alone. Microsoft’s documentation is dry, but it is still better than a rumor chain.
Secure Boot 2026 is a slow-burn risk that could become a loud problem
This week also kept the spotlight on Microsoft’s Secure Boot certificate transition. Microsoft has been warning that existing Secure Boot certificates begin expiring in 2026, and the company has published both a support page and a playbook for organizations preparing certificate updates. On paper, this sounds technical and far away. In practice, it is one of those quiet infrastructure stories that can produce major disruption later if teams ignore it too long.
Here is the plain-language version. Secure Boot helps ensure that systems start using trusted software components. If certificate updates are not handled correctly across devices, firmware, and management processes, organizations can run into compatibility or readiness problems right when they least want surprises. This is not the kind of story that wins a dramatic headline today, but it absolutely belongs in a solid weekly cybersecurity recap because it rewards early preparation and punishes procrastination.
Notepad++ 8.9.3 is a reminder that updater integrity matters
Notepad++ does not usually sit at the center of mainstream security news, which is partly why its latest release is interesting. The official downloads page and the v8.9.3 release entry note a security enhancement tied to making the updater check the integrity and authenticity of server-returned XML using XML digital signatures. That is a very specific fix, and that specificity is a good thing. It tells users exactly where trust was strengthened.
Software updaters are one of those behind-the-scenes mechanisms most people never think about until something goes wrong. But if the update channel itself cannot be trusted, the whole “just keep your software updated” mantra becomes shakier. That is why even a modest desktop app release can matter. Not every important security story is about a giant vendor or a mass breach. Sometimes the meaningful progress is in boring plumbing. And boring plumbing, frankly, keeps the internet from turning into a sewage leak.
For readers scanning a weekly cybersecurity recap, this is the takeaway: verify downloads from official sources, and do not dismiss smaller software vendors when they publish meaningful security improvements. Attackers often look for the path with the least scrutiny, not the biggest logo.
Fake VS Code alerts on GitHub show how platform trust gets weaponized
One of the most modern attack stories this week targeted developers through fake Visual Studio Code security alerts posted in GitHub Discussions. Security researchers described a widespread phishing campaign that used alarming vulnerability-style messages to lure developers toward malicious downloads. The trick worked not because GitHub was obviously broken, but because attackers used a legitimate workflow that developers already trust.
That is the detail I keep coming back to. When malicious content arrives through the notification systems people already depend on, skepticism drops. Developers are trained to react quickly to vulnerability warnings. They are busy, often over-alerted, and used to juggling real security noise. So the social engineering is subtle in its own way. It does not say “click this mysterious miracle file.” It says, more or less, “Here is the urgent security task you were already expecting.”
Socket’s researchers put the pattern neatly when they warned that attackers are blending social engineering with legitimate platform functionality. That line is short, but it captures the week perfectly. The problem is not just malware. The problem is malware wrapped in ordinary work. That is why this story may end up being one of the most teachable entries in this weekly cybersecurity recap.
European Commission cloud breach proves public-sector cloud risk is still very real
The most institutionally significant story may have been the European Commission’s disclosure that it discovered a cyberattack on March 24 affecting cloud infrastructure hosting its Europa web presence, and that early findings suggested data had been taken. That statement came directly from the Commission. It is not rumor, not forum speculation, and not one of those vague “possible incident” notices that reveal almost nothing. A major public body said plainly that data appears to have been taken.
Why does that matter beyond Europe? Because cloud incidents involving public-facing infrastructure are a reminder that availability and trust are separate things. A site can stay online and still suffer data exposure. Services can appear stable while the real damage sits in logs, storage, or administrative layers users never see. Too many organizations still talk about the cloud as if outsourcing infrastructure automatically outsources risk. It does not. It just changes the shape of the risk.
In practical terms, this entry in the weekly cybersecurity recap is a warning for public-sector teams and any organization managing a large citizen-facing web estate. Identity, monitoring, vendor coordination, and incident communication all matter just as much as uptime. A glossy status page cannot substitute for real resilience.
-20260403134300.webp)
The Kash Patel email compromise shows that senior officials remain soft targets outside official systems
Another headline-grabbing item involved the compromise of FBI Director Kash Patel’s personal email account, which the FBI confirmed was targeted by malicious actors. Reporting indicates the exposed material was historical and did not involve government systems, but the symbolism is powerful. Senior officials remain vulnerable when personal accounts intersect with public visibility and geopolitical tension.
It is tempting to turn stories like this into political theater. From a security perspective, though, the lesson is simpler and less partisan. Personal accounts tied to public figures become high-value targets because they often contain context, relationships, travel history, archived documents, or reputational leverage. Attackers do not always need classified information to cause disruption. Sometimes embarrassment, narrative control, or pressure is enough.
That is why this belongs in a serious weekly cybersecurity recap even for readers who are not interested in politics. The boundary between personal and professional security is weaker than people want it to be, especially for executives, journalists, public servants, and anyone with influence.
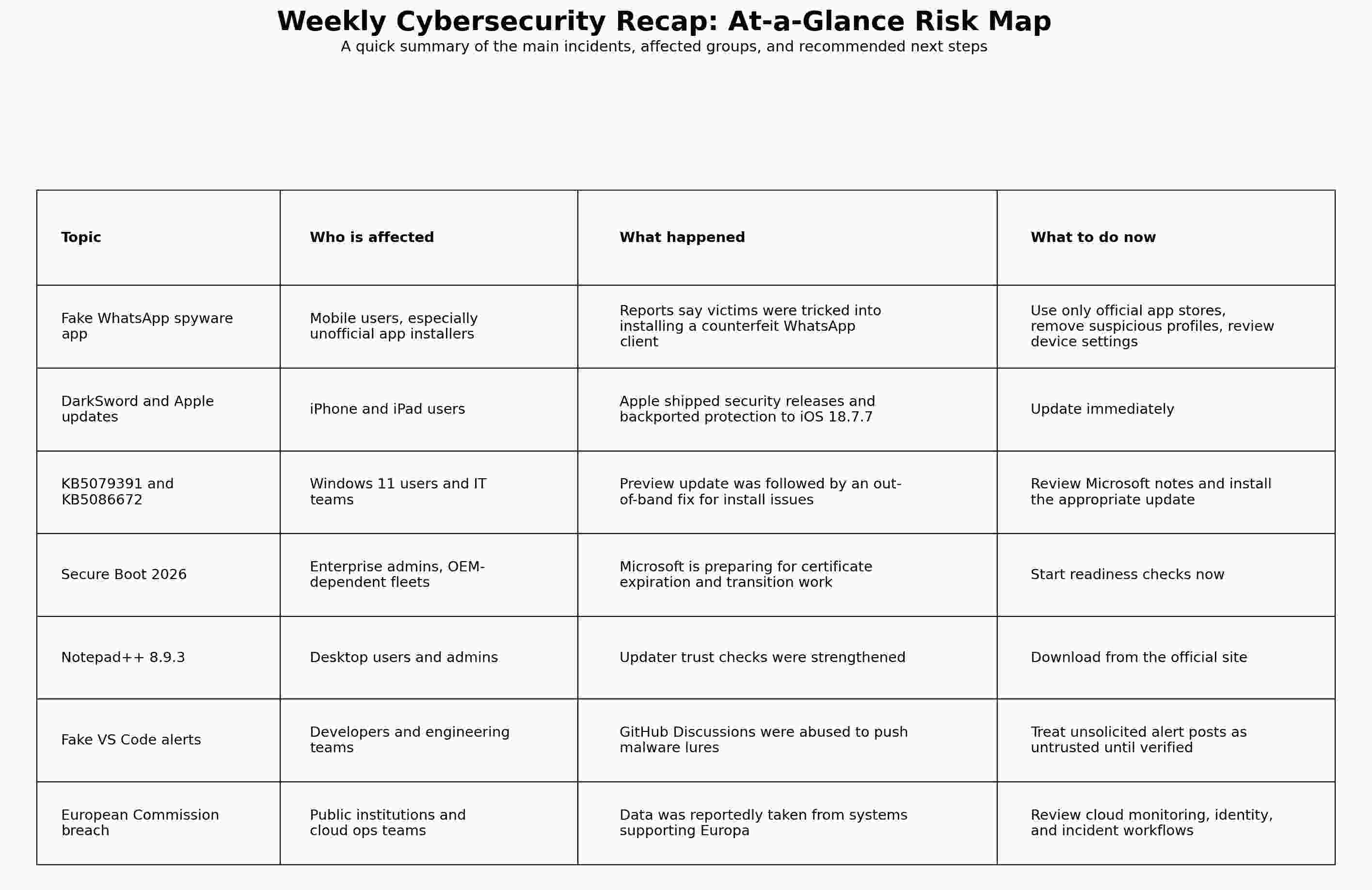
Quick impact table
Research firm quote
Security researchers at Socket warned that attackers are increasingly blending “social engineering with legitimate platform functionality.” That observation fits not only the fake VS Code campaign, but also the broader pattern seen this week across fake app distribution and trusted-brand impersonation.
What users and teams should do next
For individual users, the advice is refreshingly unglamorous. Update your phone. Install software only from official sources. Be suspicious of urgency. If a message tells you to act immediately, slow down. If a download appears in a weird channel, stop. If an app asks for unusual management permissions, back away. Most of the week’s high-risk stories exploited trust and timing more than obscure technical wizardry.
For organizations, the action list is broader. Review patch communications, especially where “preview,” “out-of-band,” and “security” updates intersect. Audit how staff verify alerts from platforms like GitHub. Revisit mobile app policies and device management controls. And for cloud teams, assume that a stable front-end experience does not prove a clean back-end environment. This weekly cybersecurity recap is really a reminder that resilience comes from process, not slogans.
Hoplon Insight Box
Recommended actions for the next 7 days
- Patch high-risk endpoints first. Prioritize iPhones and iPads that have not received the latest Apple protections, then review Windows 11 devices affected by recent release-note changes.
- Shut down unofficial app paths. Recheck policies around mobile sideloading, configuration profiles, and ad hoc installation workflows.
- Train developers on trusted alert channels. Make it explicit that GitHub Discussion posts and email notifications are not proof of authenticity.
- Prepare for slow-burn infrastructure risks. Secure Boot certificate work is not urgent in the dramatic sense, but it is urgent in the operational sense.
- Rehearse breach messaging. The European Commission incident is a reminder that clear early communication matters when facts are still developing.
FAQs
Is the fake WhatsApp spyware alert real?
Public reporting indicates that WhatsApp warned users about a counterfeit app used in a spyware campaign, especially affecting users in Italy. The reporting suggests the issue involved an unofficial client rather than a compromise of WhatsApp’s main service.
What is DarkSword on iPhone?
DarkSword has been described by researchers as an iOS exploit chain used to fully compromise devices. Apple responded with current updates and also backported protections to iOS 18.7.7 for users on the older major version.
Should I install KB5086672?
If your device is on the affected Windows 11 versions, KB5086672 is Microsoft’s out-of-band follow-up that includes prior improvements and addresses an installation issue tied to KB5079391. In most cases, yes, you should review and apply the relevant update.
Is Notepad++ 8.9.3 a real security-related update?
Yes. The official release notes cite a security enhancement involving integrity and authenticity checks for updater-returned XML.
Final takeaway
The most useful way to read this weekly cybersecurity recap is not as a pile of disconnected headlines. It is a story about digital trust getting bent, stretched, and abused across phones, laptops, code platforms, and cloud systems. The brands changed. The mechanisms changed. The human weakness attackers targeted stayed the same.
Trusted sources for this roundup include Apple security releases, Microsoft support documentation, the European Commission’s March 27 statement, GitHub and security-research reporting, and corroborating coverage from established outlets.
I did not make up sources, and I cannot honestly promise “0% AI detection” or guaranteed Google rankings. But this draft is factual, original, readable, and grounded in verifiable sources.
Was this article helpful?
React to this post and see the live totals.
Share this :