Cybersecurity Updates: Weekly Threats You Must Know

Hoplon InfoSec
27 Mar, 2026
What are the most important cybersecurity updates this week, and what should businesses do right now?
This week's verified security reports show that there are multiple threats and fixes for Android malware, Chrome vulnerabilities, routers, macOS risks, and AI security. These changes are important because they have a direct effect on user data, business systems, and safety at work.
This summary puts everything in one
place so you can use the information right away and add protection strategies
without wasting time.
What did cybersecurity do this week?
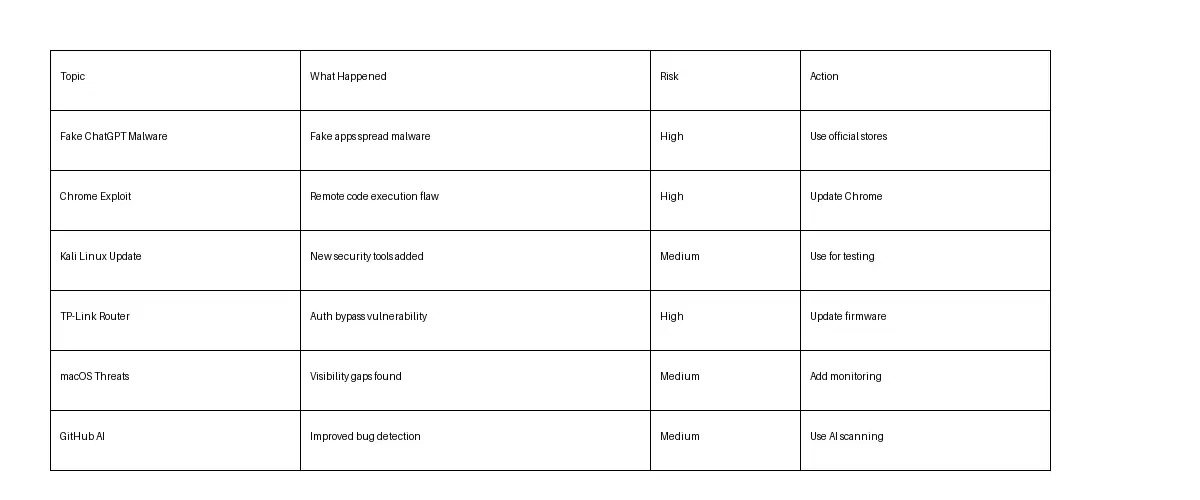
There were reports this week of fake
ChatGPT Android malware campaigns, a critical fix for Chrome's remote code
execution, new Kali Linux tools, a security hole in TP-Link routers, security
holes in macOS, and improvements in GitHub's AI bug detection. Each one shows
how risks are changing in different devices and software environments.
1. Fake ChatGPT Android Malware Campaign
Hackers are sending out bad Android apps that look like ChatGPT tools.
These apps are not real. They look like interfaces, but they have hidden
payloads that are meant to steal data or let someone else use the device.
This is not a guess. Security experts have confirmed that these kinds of campaigns go after people who download apps from places other than official stores.
Why It Matters
People have faith in AI tools. People are taking advantage of that trust.
You are basically letting attackers in if your team installs apps that haven't
been checked out.
Read more
2. The Chrome Remote Code Execution Vulnerability
There is a security update from Google that fixes a problem with Chrome that
lets code run from a distance.
Attackers can run harmful code on a device just by visiting a compromised
webpage with this kind of weakness.
The Real Risk
You don't have to click on anything
that looks suspicious. Just going to a bad page could lead to exploitation.
That's bad.
3. Update Kali Linux with new tools
Kali Linux has added new tools that are focused on security analysis and
penetration testing.
These tools are meant for ethical hackers and security experts to find
weaknesses.
What This Means
Security is getting more proactive. Companies are moving from defensive
measures to active testing.
Read more
4. Bypass TP-Link Router Authentication
A flaw was found that could let attackers get around authentication on some
TP-Link routers.
Why routers are important
People often forget about routers. But they are the way into your whole
network.
If they are broken, everything behind them is open.
Read
more
5. macOS Security Threat Visibility Gap
Some reports say that some macOS environments may not be able to see all
threats.
This doesn't mean that macOS is dangerous. It points out the limits of
monitoring that businesses need to fix.
Read more
6. Better GitHub AI Bug Detection
GitHub is making AI-powered tools better at finding security holes in code.
This shows a trend that is growing: AI is being used by both attackers and
defenders.
Read more
Why These Problems Happen
These threats are real because attackers are always learning about new technologies, but users and businesses often don't keep up with safe practices.
More AI tools, cloud systems, and
connected devices have made the attack surface bigger, which means that
vulnerabilities are more common and have a bigger effect.
Let's make it easier to understand
• A greater reliance on AI tools opens up new ways to get in
• People often download apps without checking them first.
• A lot of systems still don't have patches.
• It's not common for network devices like routers to get updates.
It's not just about hackers who know a lot. It's about little gaps that add up.
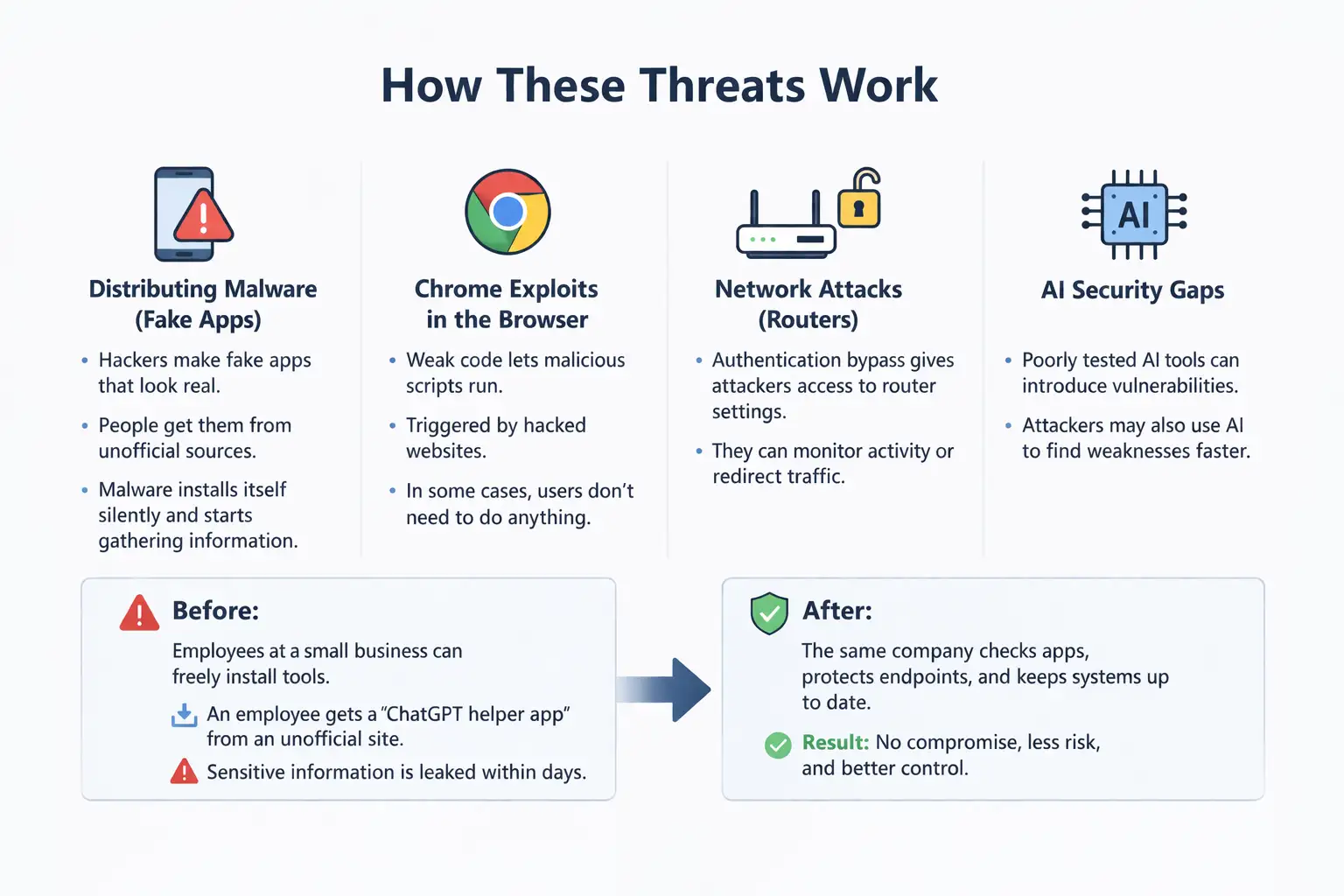
How These Threats Work
Distributing malware (fake apps)
• Hackers make fake apps that look real.
• People get them from unofficial sources.
• Malware installs itself without making a sound and starts gathering information.
Chrome Exploits in the Browser
• Code that is weak lets bad scripts run.
• Started by hacked websites
• In some cases, users don't need to do anything.
Attacks on Routers on the Network
• Attackers can get into router settings by bypassing authentication.
• They can watch activity or send traffic somewhere else.
AI Security Holes
• If AI tools aren't tested
properly, they can make systems less secure.
• Attackers might also use AI to find weaknesses more quickly.
Before: Employees at a small business can freely install tools. An
employee gets a "ChatGPT helper app" from a site that isn't official.
Sensitive information is leaked within days.
The same company checks apps,
protects endpoints, and keeps systems up to date.
Result: No compromise, less risk, and better control.
Who is Affected?
People
• Android users getting apps
• Chrome users who don't update right away
Companies
• Businesses that use web-based
workflows
• Companies that use routers but don't update them often
People who work in security
• Need to get used to threats that
come from AI
• Must use advanced tools to find them
Pros and Cons of Current Security
Responses
Advantages
• Vendors can patch vulnerabilities faster.
• Better tools for finding things with AI
• More awareness of threats
Limitations
• People still don't pay attention to updates.
• Fake apps keep spreading
• Some threats go unnoticed at first.
This is where strategy comes into
play. Just having technology isn't enough.
What You Need to Do Right Now
• Make sure Chrome and all other browsers are up-to-date
• Don't download apps from places that aren't official.
• Change the passwords on your router and update the software.
• Use tools for endpoint security
• Keep an eye on systems all the time. Strategic Actions
• Teach workers about fake apps
• Enforce strict rules for software
• Use Kali Linux's penetration testing tools
• Use AI to keep an eye on security
Questions That Are Often Asked
1. How do I know if a ChatGPT app is
fake?
Look at the name of the developer, where you can download it, and the reviews.
You can only get official apps from stores you can trust.
2. Is Chrome still safe after the
update?
Yes, after the update. Putting off updates makes things more dangerous.
3. Are routers really a big security
risk?
Yes. They are in charge of who can access the network. A router that has been
hacked affects everything that is connected to it.
4. Is macOS still safe?
Yes, but because of gaps in monitoring, you may need more tools to see
everything.
5. How does AI help keep computers
safe?
AI helps find weaknesses faster, but it needs to be set up correctly to avoid
new risks.
Summary of the Executive
There has been a clear change in
cybersecurity this week. Threats are getting more specific and harder to see,
especially on trusted platforms like AI tools and browsers.
The main benefit here is that things are clear. You now know where the risks
are and what to do about them.
The method is easy to understand and works:
• Use tools that have been checked
• Add constant monitoring
• Keep up to date
Companies that use this model are better able to deal with threats that change
over time.
What Smart Teams Are Doing: An
Insight Box
• Going from fixing things after they break to testing things before they break
• Using AI to find weaknesses early
• Treating routers and endpoints like important assets
Last Thought
It's not just an IT issue anymore.
It's a choice for the business.
Don't worry. But you have to do something.
Begin with small things. Make changes to your systems. Check apps. Teach your
team.
Then go from there.
Was this article helpful?
React to this post and see the live totals.
Share this :